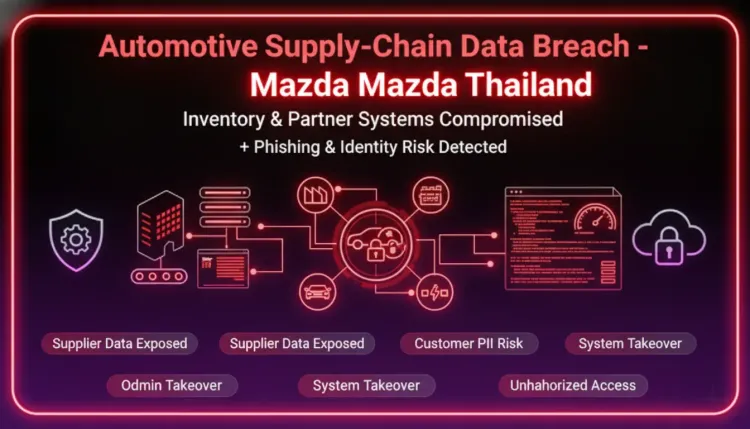
Mazda data breach: Thailand system exposed 692 records | 2026
Executive Summary
Mazda disclosed that unauthorized access to an internal spare-parts inventory management system in Thailand occurred in mid-December 2025, with 692 individuals potentially affected. According to the company, the exposed data may include Mazda user IDs, names, email addresses, company names, and business partner IDs tied to employees, affiliated entities, and partners. Mazda said regular customer data was not stored in the affected system. No confirmed secondary damage had been reported at disclosure time, but the company warned affected individuals to watch for suspicious emails. For defenders, the immediate takeaway is clear: even when customer records are excluded, employee and partner identifiers can still enable phishing, impersonation, and supply-chain targeting.
What happened?
- Mid-December 2025: Unauthorized access reportedly occurred against an internal management system used for spare-parts inventory handling in Thailand.
- During investigation: Mazda said it identified potential exposure involving 692 individuals.
- Affected data: Reportedly included user IDs, names, email addresses, company names, and business partner IDs.
- Scope clarification: Mazda stated that regular customer data was not stored in the affected system.
- Regulatory response: The company said it notified the relevant Personal Data Protection Committee and worked with third-party specialists.
- Current status: No secondary damage had been confirmed at the time of disclosure.
Unconfirmed: The disclosure did not publicly detail the specific vulnerability, intrusion path, attacker identity, or dwell time beyond the reported incident window.
Who is affected?
The impacted population appears to be limited to employees, affiliated entities, and business partners connected to Mazda's Thailand spare-parts operations. Based on Mazda's disclosure, regular customers were not affected because their data was not stored in the compromised system.
The main exposure risk is therefore not consumer fraud at scale, but targeted abuse of internal and third-party business identity data. That can include phishing against staff, impersonation of suppliers, and broader reconnaissance of logistics or procurement workflows.
Initial access & kill chain
Mazda has not publicly described the full intrusion chain, so the sequence below should be treated as a high-confidence functional model, not confirmed attacker tradecraft.
- Initial access: Attackers exploited one or more security weaknesses in an externally reachable or insufficiently protected inventory management environment.
- Access to application data: The threat actor obtained unauthorized access to business records linked to staff and partners.
- Collection: Identity and relationship data such as email addresses, names, and partner identifiers were exposed.
- Actions on objectives: The most likely downstream use is phishing, impersonation, and follow-on intrusion attempts rather than immediate customer account abuse.
| ATT&CK Stage | Likely Technique | Confidence |
|---|---|---|
| Initial Access | Exploit Public-Facing Application (T1190) or Valid Accounts (T1078) | Low |
| Discovery | Account Discovery (T1087) / Network Service Scanning (T1046) | Low |
| Collection | Data from Information Repositories (T1213) | Medium |
| Actions on Objectives | Phishing for Information (T1598) / Trusted Relationship abuse (T1199) | Medium |
Indicators and detection
Defenders should focus on signs of abnormal access to low-profile business applications and follow-on phishing or supplier impersonation.
EDR
- Investigate unusual administrative or browser activity on hosts that can access spare-parts or procurement systems.
- Review authentication patterns for users tied to inventory, logistics, and partner-management workflows.
- Hunt for credential theft artifacts after suspicious email delivery to affected populations.
Email security
- Watch for phishing using Mazda, supplier, logistics, invoice, or procurement themes.
- Flag lookalike sender domains targeting employees or known partners.
- Review whether affected identities were later used in reply-chain or business email compromise attempts.
Identity
- Review successful logins to the affected application from unusual IP ranges, ASNs, or geographies.
- Reset or challenge credentials for users with access to the impacted system if exposure cannot be ruled out.
- Check for suspicious MFA fatigue, password reset activity, or newly enrolled authenticators.
Network / proxy / DNS
- Review access logs for the affected application around mid-December 2025 and immediately afterward.
- Look for anomalous traffic volume, enumeration behavior, or repeated requests against login and data export functions.
- Monitor for outbound connections or access attempts linked to newly observed phishing domains.
Example query pattern (Splunk SPL)
splindex=web OR index=auth ("inventory" OR "spare-parts" OR "partner") ( action=login OR uri_path="*login*" OR uri_path="*export*" ) | stats count dc(src_ip) values(src_ip) values(user) values(uri_path) by app, action | sort - count
Containment & remediation checklist
🔴 Immediate containment (0–24h)
- Confirm whether the affected application is still externally reachable and restrict access if not essential.
- Reset credentials and revoke active sessions for accounts with administrative or privileged access.
- Review access logs for the incident window and preserve forensic evidence.
- Notify affected employees and partners about elevated phishing and impersonation risk.
- Block known suspicious IPs, domains, or sessions tied to the incident if identified.
- Validate whether any data export, bulk query, or account enumeration actions occurred.
- Review third-party access paths and temporarily narrow access to approved source networks only.
🟠 Hardening (24–72h)
- Patch or remediate the exploited weakness once confirmed.
- Enforce MFA for all access paths into inventory, procurement, and partner systems.
- Apply network segmentation and IP allowlisting for sensitive business applications.
- Audit service accounts, API keys, and stale partner access.
- Improve alerting for anomalous access to back-office systems that are often under-monitored.
- Review mail security controls for supplier impersonation and invoice fraud scenarios.
🟡 Longer-term controls (1–4 weeks)
- Reclassify operational inventory and logistics systems as security-sensitive where they store identity or partner data.
- Minimize stored personal and third-party identifiers where not operationally necessary.
- Build playbooks for partner-notification, phishing response, and trusted-relationship abuse.
- Test incident response procedures against attacks that start from non-customer business systems.
- Conduct exposure reviews of other low-profile applications with similar data characteristics.
- Align breach assessment and notification workflows with Thailand PDPA requirements.
Strategic analysis
This incident is a useful reminder that breach severity should not be judged only by whether customer data was exposed. Internal systems used for inventory, procurement, and partner coordination often hold exactly the relationship data attackers need to launch effective phishing or business process abuse.
In practice, employee and partner directories can support trusted-relationship attacks, supplier impersonation, invoice fraud, and staged credential theft. For automotive and manufacturing organizations, those risks extend beyond privacy exposure into operational disruption and broader supply-chain security concerns.
What happened?
Mazda disclosed unauthorized access to an internal spare-parts inventory management system in Thailand, with 692 individuals potentially affected.
Who is affected?
According to Mazda, the affected population includes employees, affiliated entities, and business partners. Regular customer data was reportedly not stored in the system.
What data may have been exposed?
Mazda said the exposed information may include user IDs, names, email addresses, company names, and business partner IDs.
How do I know if I'm impacted?
Organizations should review whether their staff or partners had accounts or records in the affected Thailand inventory environment and watch for targeted phishing.
What should defenders do first?
Prioritize access review, credential resets for privileged users, external exposure reduction, and phishing warnings to affected populations.
Is the incident still ongoing?
Public reporting did not confirm ongoing attacker activity, but Mazda did not disclose enough technical detail to independently rule out residual risk.