Threat Hunting & Intel
DAEMON Tools supply-chain attack turns trusted installers into a malware delivery path
DAEMON Tools supply-chain attack turns trusted installers into a malware delivery path The most important part of the DAEMON Tools incident is not that malware...
Lucas Oliveira
Research
CVE-2026-41940 turns exposed cPanel and WHM servers into control-plane takeover targets
CVE-2026-41940 turns exposed cPanel and WHM servers into control-plane takeover targets CVE-2026-41940 is a critical authentication bypass in cPanel and WHM, an...
Lucas Oliveira
Research
Firestarter leaves patched Cisco firewalls at continued risk
Firestarter leaves patched Cisco firewalls at continued risk A newly detailed persistence mechanism called Firestarter changes the defender story around last ye...
Lucas Oliveira
Research
AgingFly campaign hits Ukrainian government and hospital networks
AgingFly campaign hits Ukrainian government and hospital networks A newly reported campaign centered on the AgingFly backdoor is a reminder that targeted intrus...
Lucas Oliveira
Research
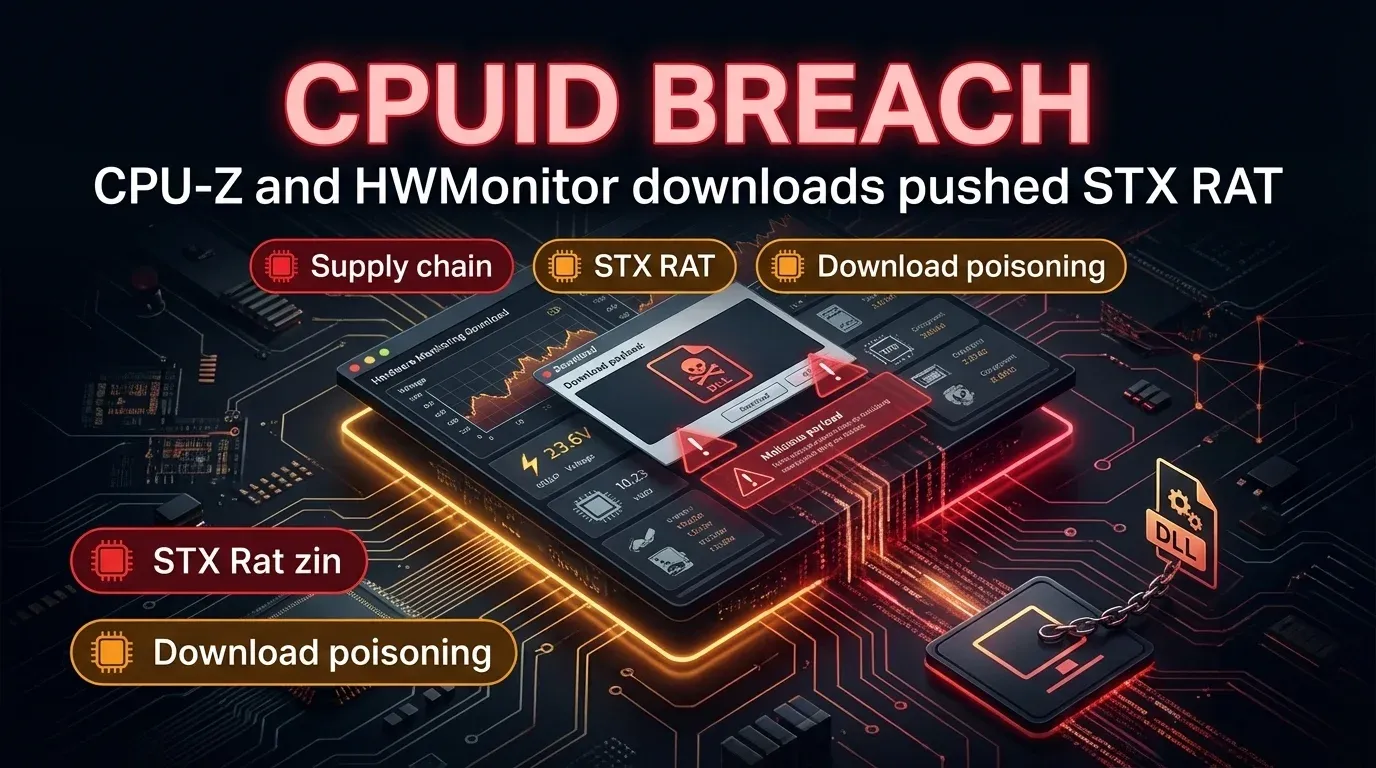
CPUID breach turned CPU-Z and HWMonitor into a malware delivery path
CPUID breach turned CPU-Z and HWMonitor into a malware delivery path Executive summary A compromise of the CPUID website briefly turned trusted download links f...
Lucas Oliveira
Research
Iranian PLC Attacks Disrupt U.S. Critical Infrastructure
Iranian PLC Attacks Disrupt U.S. Critical Infrastructure Executive Summary Iranian-affiliated [advanced persistent threat](https://invaders.ie/resources/glossar...
Lucas Oliveira
Research
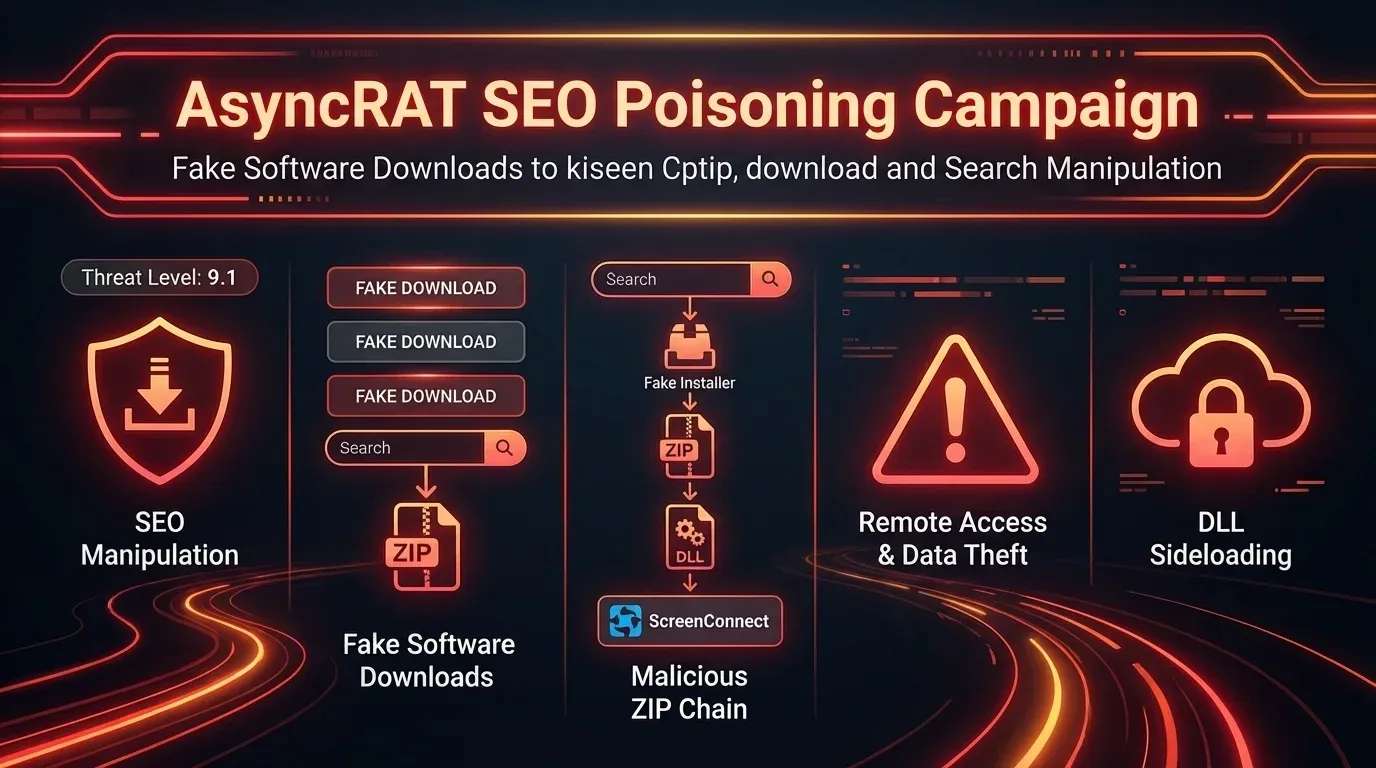
AsyncRAT SEO Poisoning Campaign Targets Software Downloads
AsyncRAT: SEO Poisoning Hits Software Downloads | 2026 Executive Summary In March 2026, NCC Group and FOX-IT disclosed that an unknown threat actor had been run...
Lucas Oliveira
Research
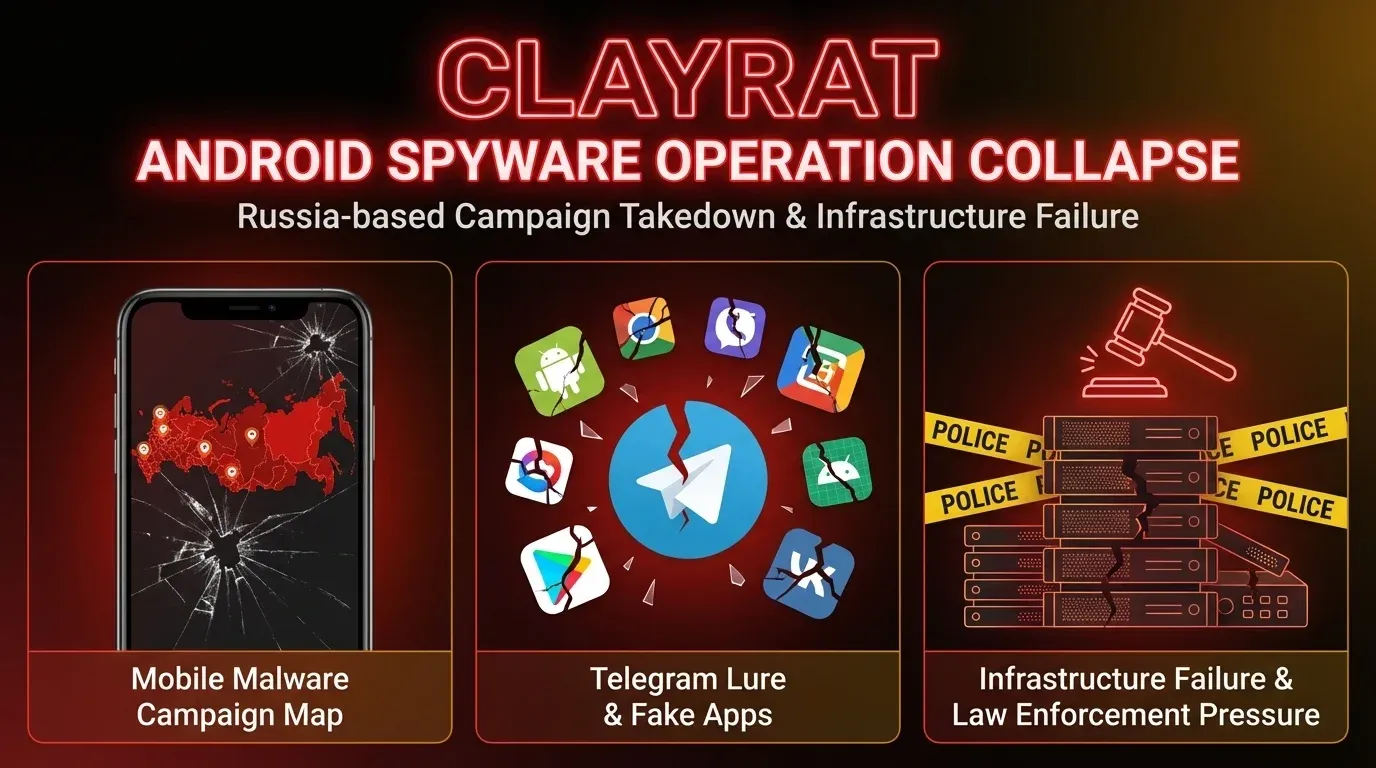
ClayRat Android spyware collapse after arrest in Russia
ClayRat: Android spyware operation collapses after arrest | 2026 Executive Summary ClayRat is an Android spyware operation that targeted users in Russia and app...
Lucas Oliveira
Research
Namibia Airports Company breach claim raises admin-access risk
Namibia Airports Company breach claim raises admin-access risk | 2026 Executive Summary Namibia Airports Company (NAC) disclosed that it detected a cybersecurit...
Lucas Oliveira
Research
GlassWorm Shifts to Transitive Open VSX Dependencies in Developer Supply-Chain Push
GlassWorm Shifts to Transitive Open VSX Dependencies in Developer Supply-Chain Push GlassWorm is no longer just a story about obviously malicious extensions. Th...
Lucas Oliveira
Research
Cline CLI 2.3.0 supply chain attack silently installed OpenClaw on developer systems
Cline CLI 2.3.0 supply chain attack silently installed OpenClaw on developer systems Executive summary The Cline CLI supply chain incident is a practical remind...
Lucas Oliveira
Research
FBI seizes Handala sites after destructive Stryker hack
FBI seizes Handala sites after destructive Stryker hack | 2026 Executive Summary The FBI and U.S. Department of Justice have seized two websites linked to Handa...
Lucas Oliveira
Research