Cloud & Application Security
CVE-2026-45829: ChromaDB Pre-Auth RCE Risk in AI Stacks
CVE-2026-45829: ChromaDB Pre-Auth RCE Risk in AI Stacks | 2026 Executive Summary CVE-2026-45829 is a critical ChromaDB flaw that can let unauthenticated attacke...
Lucas Oliveira
Research
LiteLLM SQL injection flaw puts AI gateways on the front line
LiteLLM SQL injection flaw puts AI gateways on the front line CVE-2026-42208 matters because it turns an AI gateway into a high-value choke point for attackers....
Lucas Oliveira
Research
Vishing and SSO abuse are accelerating rapid SaaS extortion
Vishing and SSO abuse are accelerating rapid SaaS extortion The most dangerous part of modern SaaS intrusions is not always malware. Sometimes it is speed, trus...
Lucas Oliveira
Research
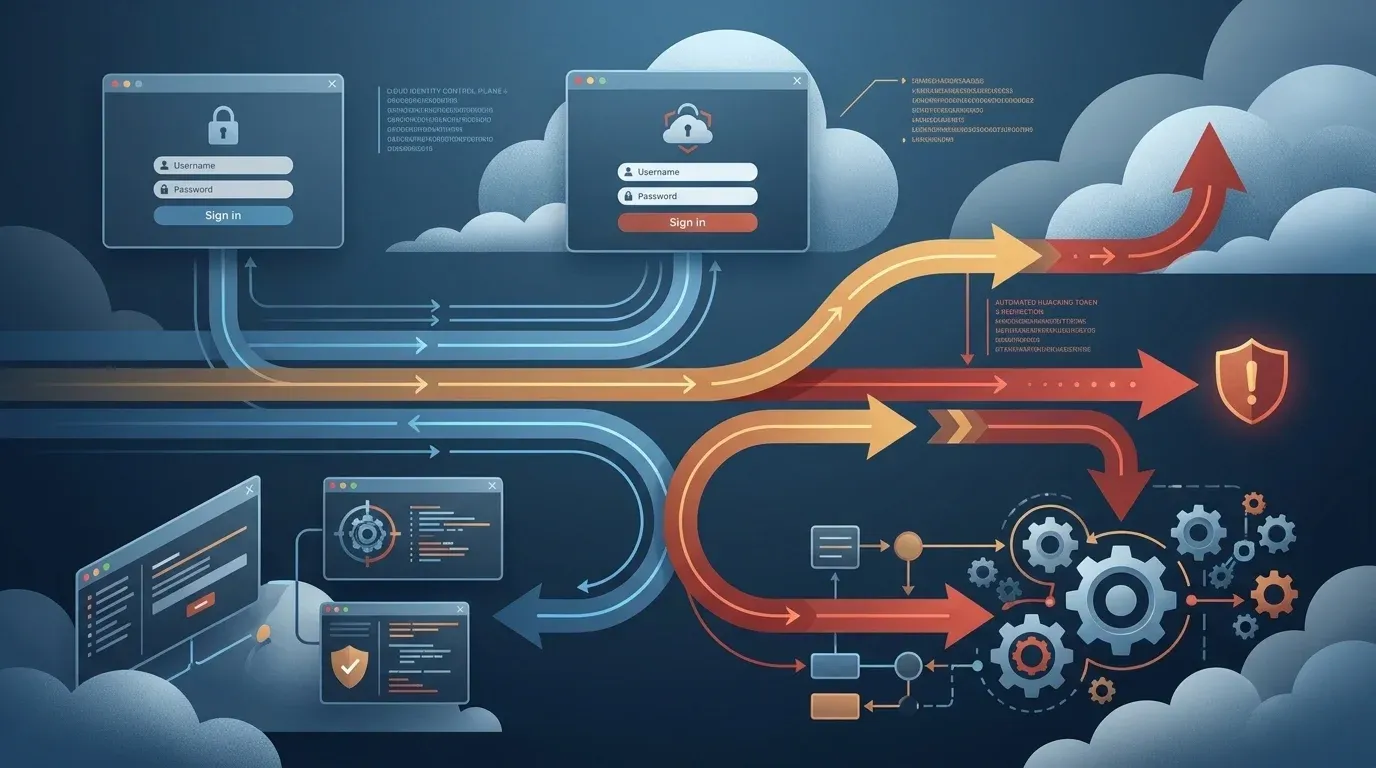
ConsentFix v3 turns Azure OAuth phishing into a scalable token theft risk
ConsentFix v3 turns Azure OAuth phishing into a scalable token theft risk ConsentFix v3 matters because it shifts Azure account compromise away from password th...
Lucas Oliveira
Research
PyTorch Lightning supply-chain compromise puts AI developer credentials at risk
PyTorch Lightning supply-chain compromise puts AI developer credentials at risk The most dangerous supply-chain incidents are not always the ones that hit opera...
Lucas Oliveira
Research
CVE-2026-42208 turns exposed LiteLLM gateways into a secrets exposure risk
CVE-2026-42208 turns exposed LiteLLM gateways into a secrets exposure risk CVE-2026-42208 is a critical SQL injection flaw in LiteLLM's proxy API key verificati...
Lucas Oliveira
Research
Lovable Incident Raises Cross-Tenant Data Exposure Concerns for AI Development Platforms
Lovable Incident Raises Cross-Tenant Data Exposure Concerns for AI Development Platforms Lovable, an AI platform used to build and iterate software projects, is...
Lucas Oliveira
Research
CVE-2026-5752 turns the Terrarium sandbox into a root-level escape risk
CVE-2026-5752 turns the Terrarium sandbox into a root-level escape risk A critical flaw in Terrarium, tracked as CVE-2026-5752, deserves attention well beyond a...
Lucas Oliveira
Research
Malicious Chrome extensions turn OAuth tokens into enterprise risk
Malicious Chrome extensions turn OAuth tokens into enterprise risk A newly reported cluster of malicious Chrome Web Store extensions is a useful warning for def...
Lucas Oliveira
Research
CVE-2026-39987 puts exposed Marimo notebooks on a fast credential-theft path
CVE-2026-39987 puts exposed Marimo notebooks on a fast credential-theft path CVE-2026-39987 is a sharp reminder that smaller developer and data-science platform...
Lucas Oliveira
Research
CVE-2026-33017: Langflow RCE Hits Exposed AI Pipelines
CVE-2026-33017: Langflow RCE Hits Exposed AI Pipelines | 2026 CVE-2026-33017 is a critical Langflow flaw that turns a public-flow convenience feature into unaut...
Lucas Oliveira
Research
Critical n8n Flaws Enable RCE and Credential Exposure
Critical n8n flaws enable RCE and credential exposure | 2026 Executive Summary Two critical n8n flaws disclosed in March 2026 significantly raise risk for both...
Lucas Oliveira
Research