Stay Protected with Expert Guidance
In-depth security strategies and technical analysis to keep your infrastructure resilient against evolving digital threats.
Explore Intelligence
Featured Posts
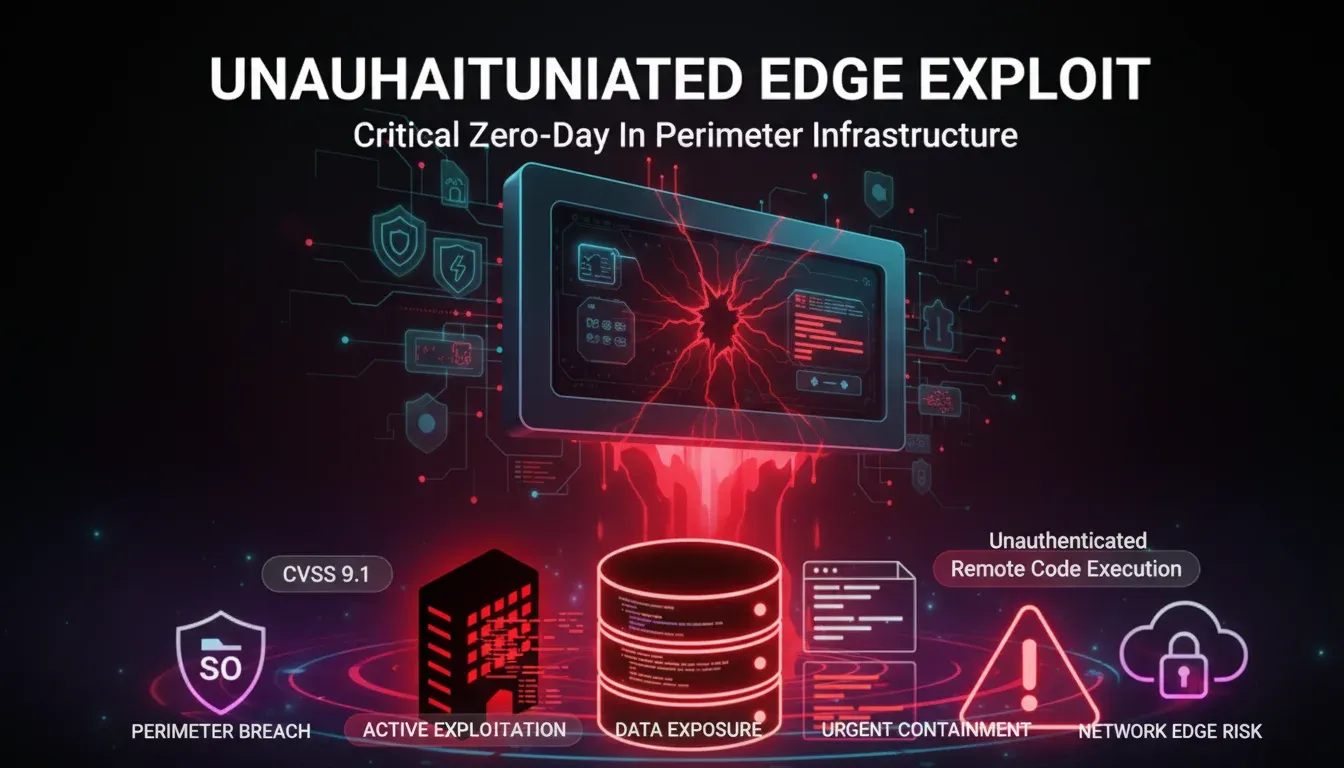
CVE-2026-0300 puts exposed PAN-OS User-ID portals on a zero-day attack path
CVE-2026-0300 puts exposed PAN-OS User-ID portals on a zero-day attack path A critical point in the new PAN-OS warning is that defenders are not looking at a ro...
Lucas Oliveira
Research
DAEMON Tools supply-chain attack turns trusted installers into a malware delivery path
DAEMON Tools supply-chain attack turns trusted installers into a malware delivery path The most important part of the DAEMON Tools incident is not that malware...
Lucas Oliveira
Research
Vishing and SSO abuse are accelerating rapid SaaS extortion
Vishing and SSO abuse are accelerating rapid SaaS extortion The most dangerous part of modern SaaS intrusions is not always malware. Sometimes it is speed, trus...
Lucas Oliveira
Research
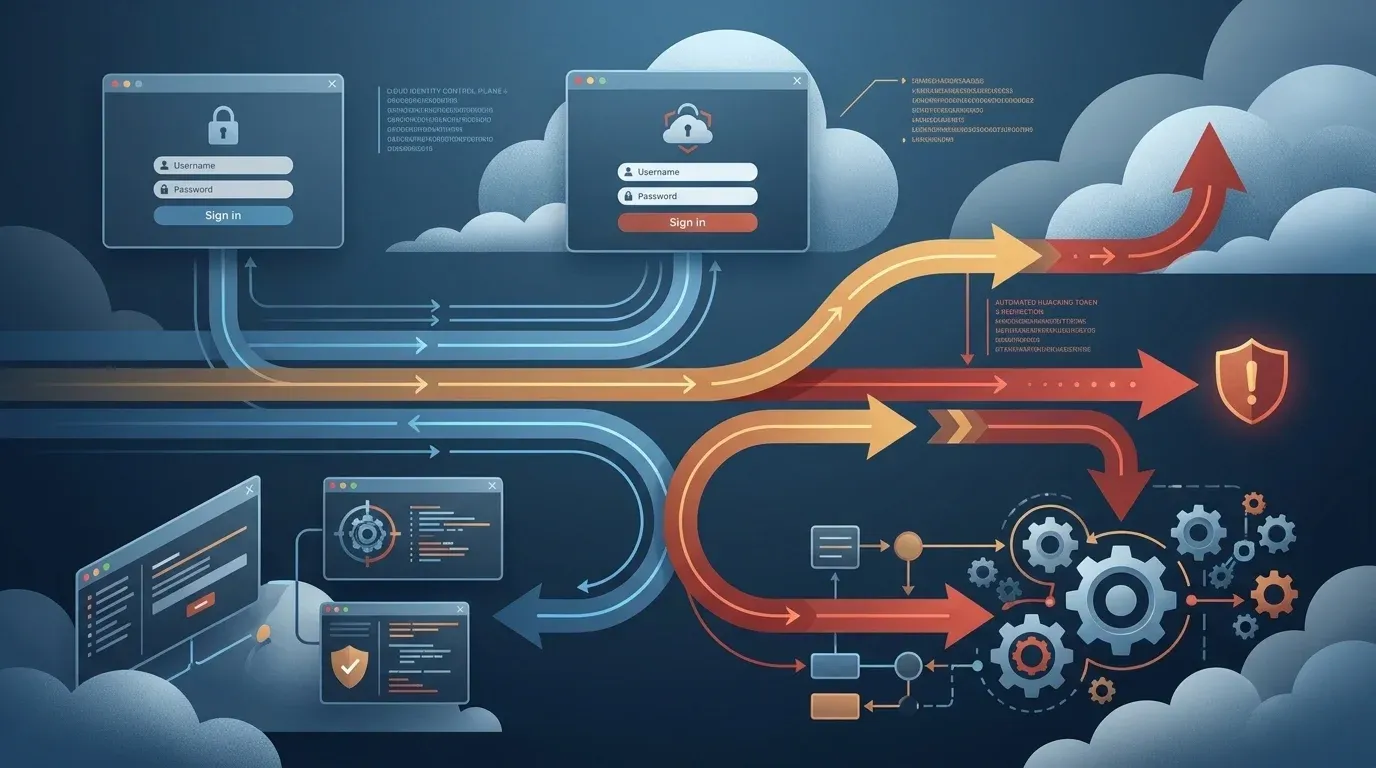
ConsentFix v3 turns Azure OAuth phishing into a scalable token theft risk
ConsentFix v3 turns Azure OAuth phishing into a scalable token theft risk ConsentFix v3 matters because it shifts Azure account compromise away from password th...
Lucas Oliveira
Research
CVE-2026-42208 turns exposed LiteLLM gateways into a secrets exposure risk
CVE-2026-42208 turns exposed LiteLLM gateways into a secrets exposure risk CVE-2026-42208 is a critical SQL injection flaw in LiteLLM's proxy API key verificati...
Lucas Oliveira
Research
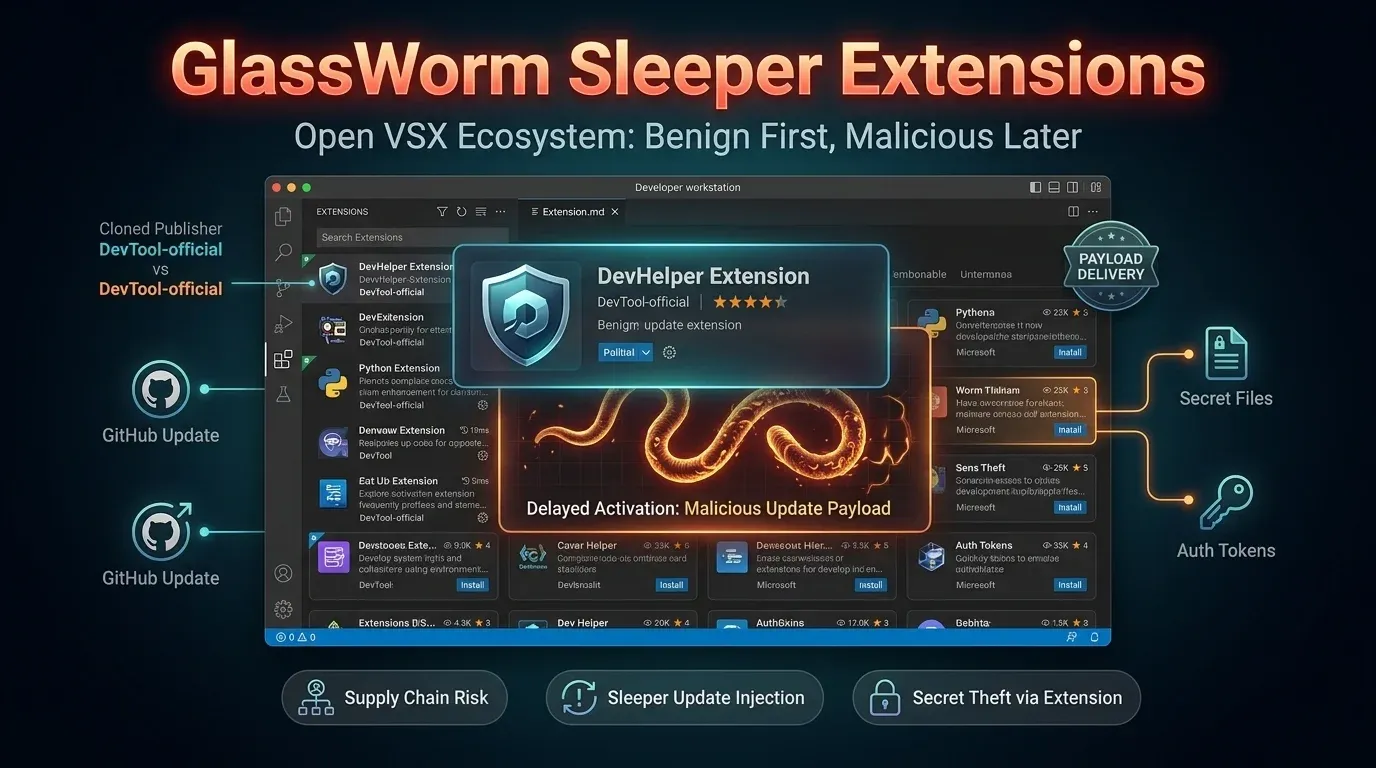
GlassWorm sleeper extensions turn Open VSX updates into a malware delivery path
GlassWorm sleeper extensions turn Open VSX updates into a malware delivery path The newest GlassWorm wave matters because it turns the normal extension update p...
Lucas Oliveira
Research
CVE-2026-33032 lets attackers take over exposed nginx-ui servers
CVE-2026-33032 lets attackers take over exposed nginx-ui servers CVE-2026-33032 is the kind of [vulnerability](https://invaders.ie/resources/glossary/vulnerabil...
Lucas Oliveira
Research
Firestarter leaves patched Cisco firewalls at continued risk
Firestarter leaves patched Cisco firewalls at continued risk A newly detailed persistence mechanism called Firestarter changes the defender story around last ye...
Lucas Oliveira
Research
Pack2TheRoot flaw puts Linux systems with PackageKit on a local root path
Pack2TheRoot flaw puts Linux systems with PackageKit on a local root path The newly disclosed Pack2TheRoot issue, tracked as CVE-2026-41651, is a strong reminde...
Lucas Oliveira
Research
Bitwarden CLI npm compromise exposes CI/CD credential risk
Bitwarden CLI npm compromise exposes CI/CD credential risk A brief compromise of the Bitwarden CLI npm distribution is still a high-priority defender story beca...
Lucas Oliveira
Research
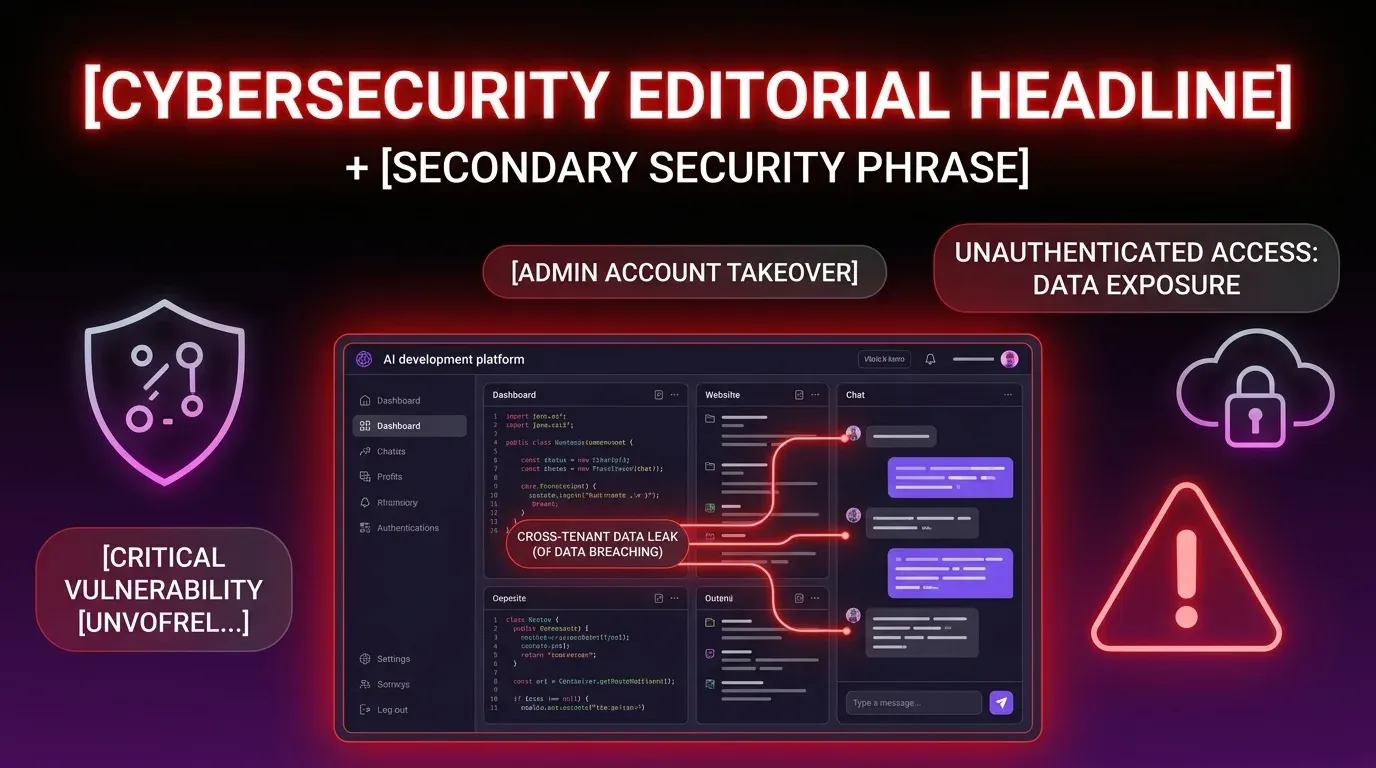
Lovable Incident Raises Cross-Tenant Data Exposure Concerns for AI Development Platforms
Lovable Incident Raises Cross-Tenant Data Exposure Concerns for AI Development Platforms Lovable, an AI platform used to build and iterate software projects, is...
Lucas Oliveira
Research
CVE-2026-5752 turns the Terrarium sandbox into a root-level escape risk
CVE-2026-5752 turns the Terrarium sandbox into a root-level escape risk A critical flaw in Terrarium, tracked as CVE-2026-5752, deserves attention well beyond a...
Lucas Oliveira
Research
CISA KEV flags Quest KACE SMA auth bypass as a high-priority risk
CISA KEV flags Quest KACE SMA auth bypass as a high-priority risk CVE-2025-32975 is the kind of issue defenders should triage quickly because it affects a manag...
Lucas Oliveira
Research
SGLang CVE-2026-5760 turns malicious GGUF models into RCE
SGLang CVE-2026-5760 turns malicious GGUF models into RCE Executive summary A newly disclosed flaw in SGLang means a malicious GGUF model file can become an exe...
Lucas Oliveira
Research