CVE-2026-20182 is not landing as a routine patch bulletin. Cisco says the flaw is already being exploited, and CISA moved it into the Known Exploited Vulnerabilities catalog almost immediately. For defenders, that combination means exposed SD-WAN control infrastructure should be treated as an active incident response problem, not just a scheduled maintenance item.
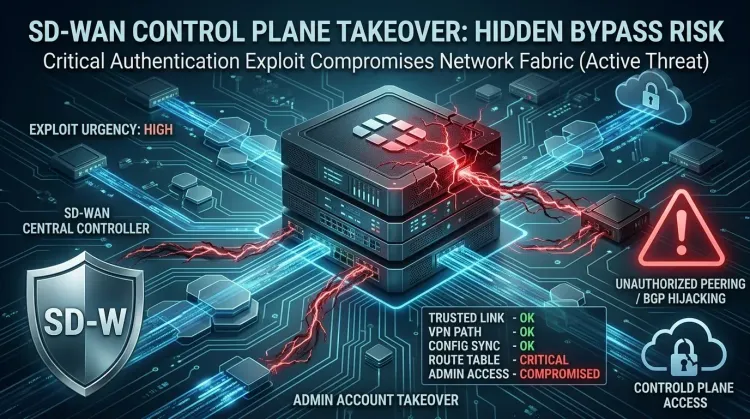
The issue is a critical authentication bypass in Cisco Catalyst SD-WAN Controller and Manager. A successful attack can give an unauthenticated remote adversary administrative foothold on infrastructure that controls routing trust, policy distribution, and encrypted site-to-site connectivity. That makes this less about a single device compromise and more about control-plane integrity across the broader WAN fabric.
What Cisco and CISA confirmed
Cisco says CVE-2026-20182 exists because peering authentication in affected SD-WAN systems does not work properly. An attacker can send crafted requests, log in as a high-privileged internal non-root account, and then access NETCONF to manipulate SD-WAN configuration.
That matters because the exposed asset is not a generic web application. It is a centralized network controller that helps define trust relationships between branch, cloud, and datacenter environments. Once an attacker reaches that layer, the risk expands from simple login bypass into network path manipulation, rogue device registration, and post-compromise persistence opportunities.
CISA's KEV listing sharpens the operational picture further. The agency added the flaw on 2026-05-14 with a remediation deadline of 2026-05-17 for federal agencies, which is usually a strong signal that defenders should compress patch and exposure-review timelines immediately.
Why this flaw stands out
1. It targets the SD-WAN trust plane
SD-WAN controllers sit close to the logic that determines how sites trust each other and how traffic is orchestrated. If an attacker can tamper with that layer, they may be able to alter routes, introduce rogue peers, or create conditions for deeper lateral movement inside the environment.
2. Active exploitation is already tied to real post-compromise behavior
The public reporting is unusually concrete. Cisco and downstream coverage indicate attackers have attempted actions such as adding SSH keys, changing NETCONF configurations, and escalating privileges after compromise. That gives defenders a better sense of what to hunt for than a vague "exploitation detected" note.
3. It fits a broader Cisco SD-WAN exploitation pattern
Rapid7 discovered the flaw while researching a previously fixed Cisco SD-WAN issue, and public reporting links the exploitation to the same broader threat activity around earlier SD-WAN bugs. That pattern matters from a threat intelligence perspective: this is not random opportunism against an obscure edge product, but continued pressure against a known enterprise access and control surface.
From auth bypass to network control risk
Cisco's description makes the attack path clear enough for defenders to reason about impact:
- An unauthenticated attacker reaches an exposed SD-WAN Controller or Manager.
- Crafted requests abuse the broken peering authentication flow.
- The attacker gains access as an internal high-privileged user.
- NETCONF access allows unauthorized configuration actions.
- Those changes can support rogue peering, infrastructure tampering, or follow-on credential and access abuse.
That is why this should be treated as more than an abstract vulnerability. In many environments, SD-WAN management components have broad visibility and significant implicit trust. Compromising them can distort the defender's assumptions about which devices belong, which routes are valid, and which management actions are legitimate.
Timeline
| Date | Event | Status |
|---|---|---|
| February 2026 | Cisco fixed the related SD-WAN issue CVE-2026-20127 | ✅ Related patch history |
| May 14, 2026 | Cisco disclosed CVE-2026-20182 and confirmed active exploitation | 🔴 Active exploitation |
| May 14, 2026 | CISA added CVE-2026-20182 to KEV | 📢 KEV listing |
| May 17, 2026 | CISA remediation due date for federal agencies | ⚠️ Urgent deadline |
What defenders should do now
Identify exposure first
Inventory every Cisco Catalyst SD-WAN Controller and Manager instance, especially any systems reachable from the internet or from less-trusted administrative zones. If teams are unsure whether exposure exists, treat that uncertainty as a finding, not a reason to wait.
Patch, but do not stop at patching
Cisco says software updates are the only complete fix. Apply the designated fixed release as fast as change control allows. But because exploitation is already confirmed, patching alone is not enough for systems that were exposed before remediation.
Hunt for rogue trust activity
Review logs for:
- unexpected peering events,
- unfamiliar system IPs,
- suspicious SSH public-key acceptance,
- abnormal configuration changes through NETCONF,
- and administrative actions originating from unknown infrastructure.
If a device shows signs of unauthorized peering or unexplained privileged access, it should be treated as potentially compromised.
Reduce exposure around the control plane
Restrict management and control-plane interfaces to trusted internal networks or explicitly authorized IP ranges. That does not replace patching, but it can meaningfully reduce the window for opportunistic exploitation and future exploit attempts.
Validate downstream impact
If compromise is suspected, expand investigation beyond the controller. Review route changes, device enrollment events, credential use, and any signs that attackers used the SD-WAN layer to pivot toward identity systems, branch infrastructure, or cloud-connected segments.
Strategic takeaway
CVE-2026-20182 matters because it hits a network orchestration layer defenders tend to trust by design. An actively exploited authentication bypass in SD-WAN control infrastructure is not just another high CVSS item in a long queue. It can undermine the assumptions that keep distributed enterprise environments manageable and segmented.
The safest operating assumption is straightforward: if a Cisco SD-WAN Controller or Manager was exposed before patching, validate both remediation status and compromise status before considering the issue closed.
Frequently Asked Questions
What is CVE-2026-20182?
CVE-2026-20182 is a critical authentication bypass vulnerability in Cisco Catalyst SD-WAN Controller and Manager. It can allow an unauthenticated remote attacker to gain administrative access to affected systems.
Why is this flaw especially important?
Because it affects SD-WAN control infrastructure rather than a low-value edge service. A compromise at that layer can influence routing trust, configuration state, and broader enterprise connectivity.
Is CVE-2026-20182 being exploited?
Yes. Cisco disclosed the flaw as actively exploited, and CISA added it to the KEV catalog on May 14, 2026.
What should teams do first?
Find every exposed SD-WAN Controller or Manager, patch to a fixed release, and review logs for unauthorized peering, suspicious SSH key activity, and abnormal privileged configuration changes.