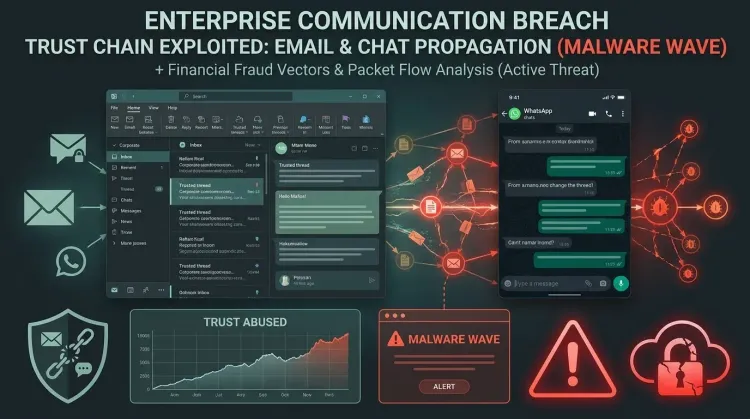
The most important detail in Elastic's new TCLBANKER research is not just that a Brazilian banking trojan targets dozens of financial brands. It is that the malware turns a victim's own WhatsApp session and Microsoft Outlook account into delivery infrastructure.
That is a serious defensive problem. When malware spreads through accounts that are already authenticated, already trusted by the recipient, and already permitted by business workflows, many conventional filters lose their advantage. The message does not look like commodity spam. It looks like it came from someone you know.
What Elastic found
Elastic Security Labs says the campaign, tracked as REF3076, uses a trojanized Logitech installer to deploy TCLBANKER. The malware chain includes a loader with extensive anti-analysis logic, a banking trojan designed to target 59 financial, fintech, and cryptocurrency platforms, and two worm modules for propagation.
Those propagation modules are what make the campaign stand out.
According to Elastic, one worm hijacks an authenticated WhatsApp Web session to message the victim's contacts. The other abuses Outlook via COM automation to send phishing emails from the victim's own mailbox. In both cases, the attacker inherits the trust, deliverability, and context of the compromised user.
That shifts the conversation from simple malware detection into social engineering, identity trust abuse, and control gaps around legitimate communications channels.
Why this campaign is more dangerous than a normal banking trojan
1. It weaponizes trusted relationships
Many phishing defenses assume suspicious infrastructure, suspicious domains, or suspicious senders. TCLBANKER disrupts that model by pushing malicious messages from real user accounts and active sessions. For the next victim, the lure arrives through a familiar channel and a familiar contact.
2. It blends fraud with worm-like spread
The core malware is built for financial theft, including credential-harvesting overlays, fake wait screens, and operator-guided fraud. But the spread mechanism behaves more like a trust-hijacking worm. That combination increases both impact and scale.
3. It degrades the value of reputation-based controls
Elastic's assessment is blunt: traditional email gateways and reputation-based defenses are poorly positioned when the message is sent from the victim's own Outlook account or automated through their active WhatsApp session. This is the kind of campaign that slips between security silos because email, messaging, endpoint, and identity all play a role.
The technical pattern defenders should pay attention to
TCLBANKER is not only noisy social engineering wrapped around a simple payload. Elastic describes a loader that uses environment-gated decryption, anti-debugging checks, ETW patching, watchdog functionality, and process restrictions to make analysis harder. Once active, the malware monitors browser URLs, activates when victims visit targeted financial sites, and opens a command-and-control channel for operator-driven actions.
It also uses full-screen WPF overlays to manipulate victims during live sessions. That matters because this is not a purely automated smash-and-grab tool. It is built to support interactive fraud and real-time user deception.
Why enterprise defenders should care
Even though the immediate target set is Brazilian banking and fintech users, the broader lesson is relevant to enterprise security teams everywhere.
Attackers keep moving toward channels that inherit legitimacy by default. If a compromised endpoint can send malware through Outlook, or a hijacked browser session can turn WhatsApp into a distribution engine, defenders need to think beyond inbound filtering. The harder problem is not only spotting the first malicious file. It is recognizing when a trusted user account starts behaving like an internal distribution point.
This matters especially for organizations with:
- heavy reliance on Outlook for internal and customer communication,
- browser-based messaging workflows,
- users handling financial approvals or high-trust external contacts,
- and security programs that still treat email, chat, endpoint, and identity telemetry as separate lanes.
What teams should do now
Watch for outbound abuse, not just inbound phishing
Look for unusual bursts of outbound email from Outlook clients, especially messages with repetitive lure structure, unexpected attachments, or sends to large contact sets. Apply the same lens to browser-based messaging activity where practical.
Correlate endpoint, identity, and messaging signals
A campaign like TCLBANKER is easiest to miss when every control only sees its own fragment. Endpoint telemetry, Office activity, browser artifacts, and messaging behavior need to be reviewed together.
Train users on trusted-channel deception
The right awareness message is not just “don't click unknown emails.” It is “trusted contacts and familiar channels can be abused after compromise.” That is a more realistic model of modern phishing and fraud.
Prepare for account containment and cleanup
If a user is hit, responders may need to contain more than one account or session. Outlook, browser sessions, messaging sessions, and local persistence all matter. This is an incident response case, not just a password reset.
Strategic takeaway
TCLBANKER shows how modern malware keeps converging with identity abuse and communications trust. The real innovation here is not the banking overlay by itself. It is the decision to use the victim's own Outlook and WhatsApp presence as a delivery system.
That is why the right defensive question is not only “can we block the payload?” It is “how quickly can we detect when trusted channels start acting on behalf of an attacker?”
What is TCLBANKER?
TCLBANKER is a Brazilian banking trojan identified by Elastic that includes anti-analysis logic, fraud overlays, and worm modules that spread via WhatsApp and Microsoft Outlook.
Why is its propagation method significant?
Because it uses authenticated user sessions and real user accounts to send malicious messages, making the campaign harder to stop with reputation and sender-based controls alone.
What should defenders prioritize?
Monitor for outbound abuse, correlate identity and endpoint telemetry, and treat trusted-channel phishing as a containment and investigation problem, not only a mail-filtering problem.