#Malware
Kazuar’s redesign turns a familiar backdoor into a harder-to-hunt botnet
Kazuar’s redesign turns a familiar backdoor into a harder-to-hunt botnet Microsoft’s latest research on Kazuar matters because it reframes the malware from a we...
Lucas Oliveira
Research
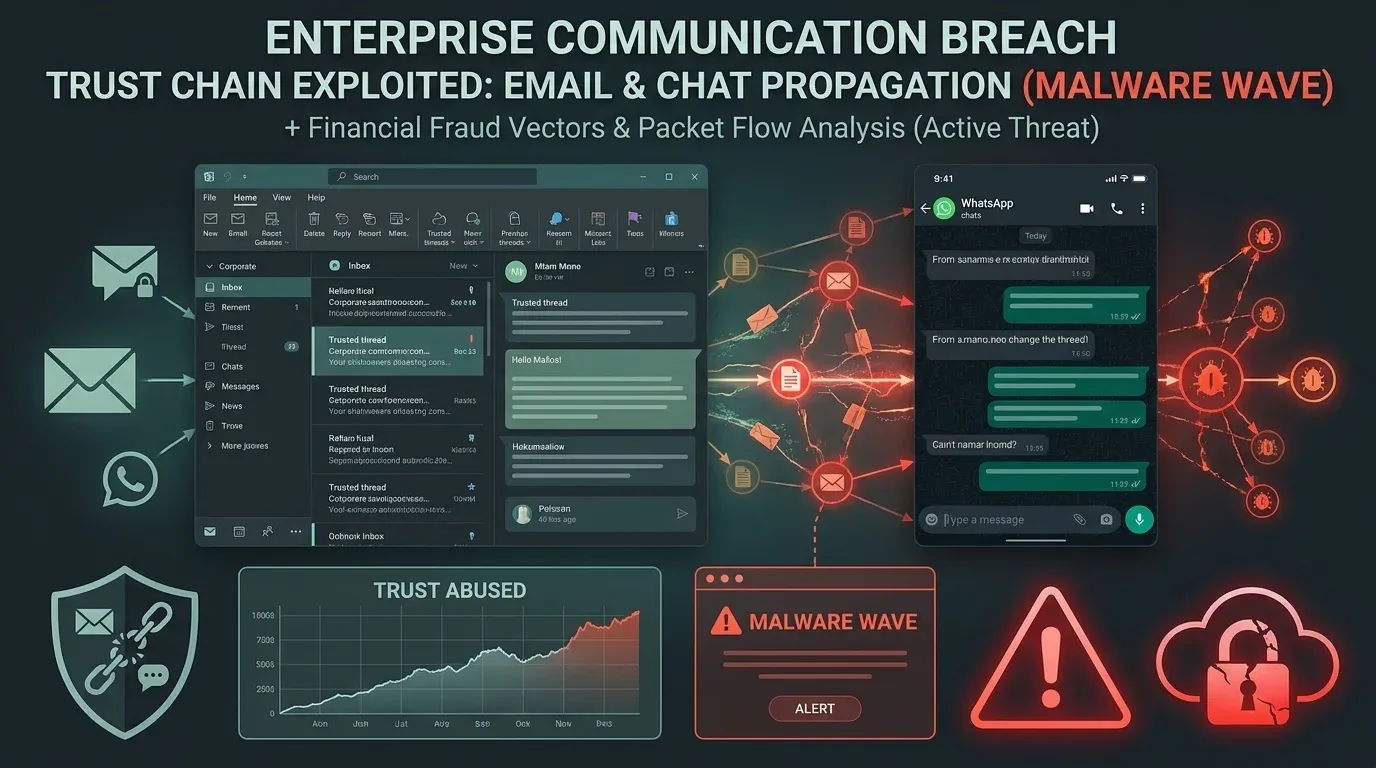
TCLBANKER turns WhatsApp and Outlook into trusted malware delivery channels
TCLBANKER turns WhatsApp and Outlook into trusted malware delivery channels The most important detail in Elastic's new TCLBANKER research is not just that a Bra...
Lucas Oliveira
Research
DAEMON Tools supply-chain attack turns trusted installers into a malware delivery path
DAEMON Tools supply-chain attack turns trusted installers into a malware delivery path The most important part of the DAEMON Tools incident is not that malware...
Lucas Oliveira
Research
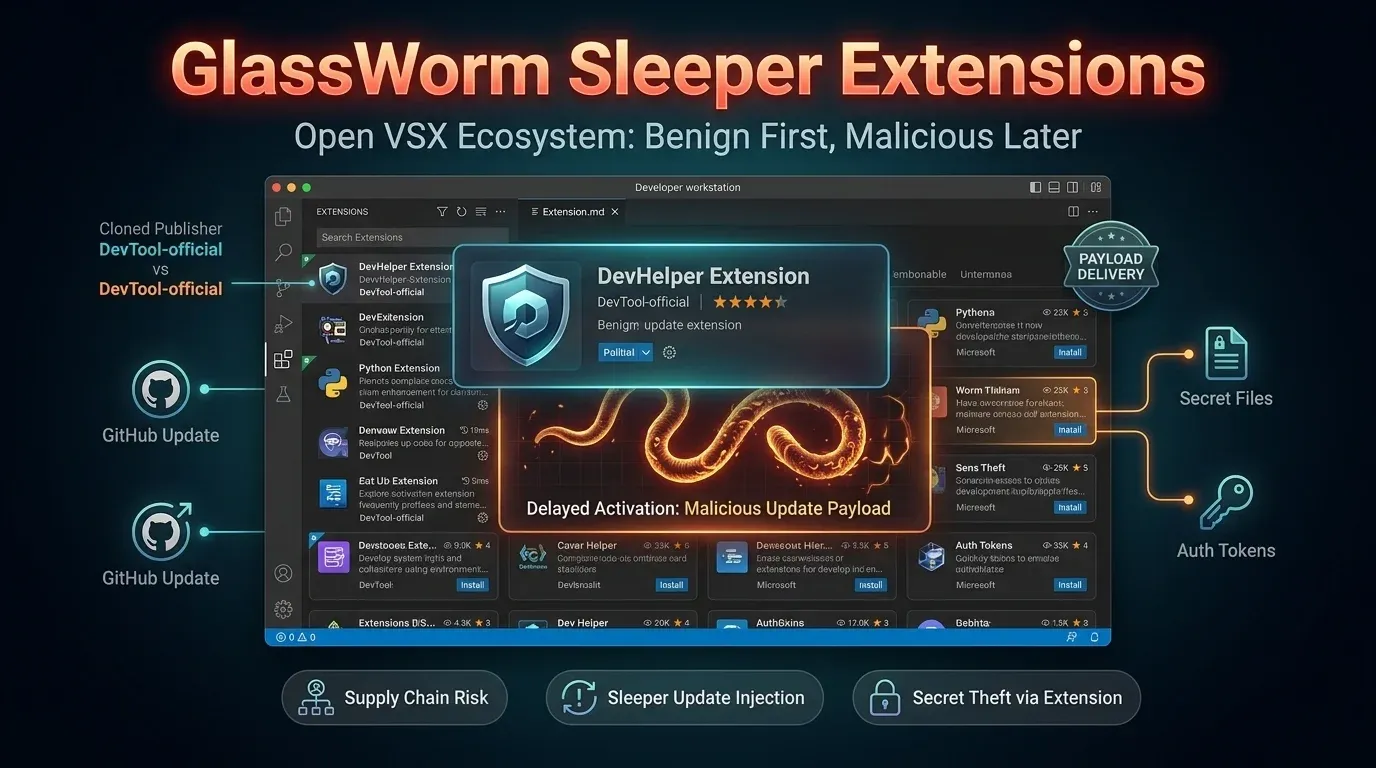
GlassWorm sleeper extensions turn Open VSX updates into a malware delivery path
GlassWorm sleeper extensions turn Open VSX updates into a malware delivery path The newest GlassWorm wave matters because it turns the normal extension update p...
Lucas Oliveira
Research
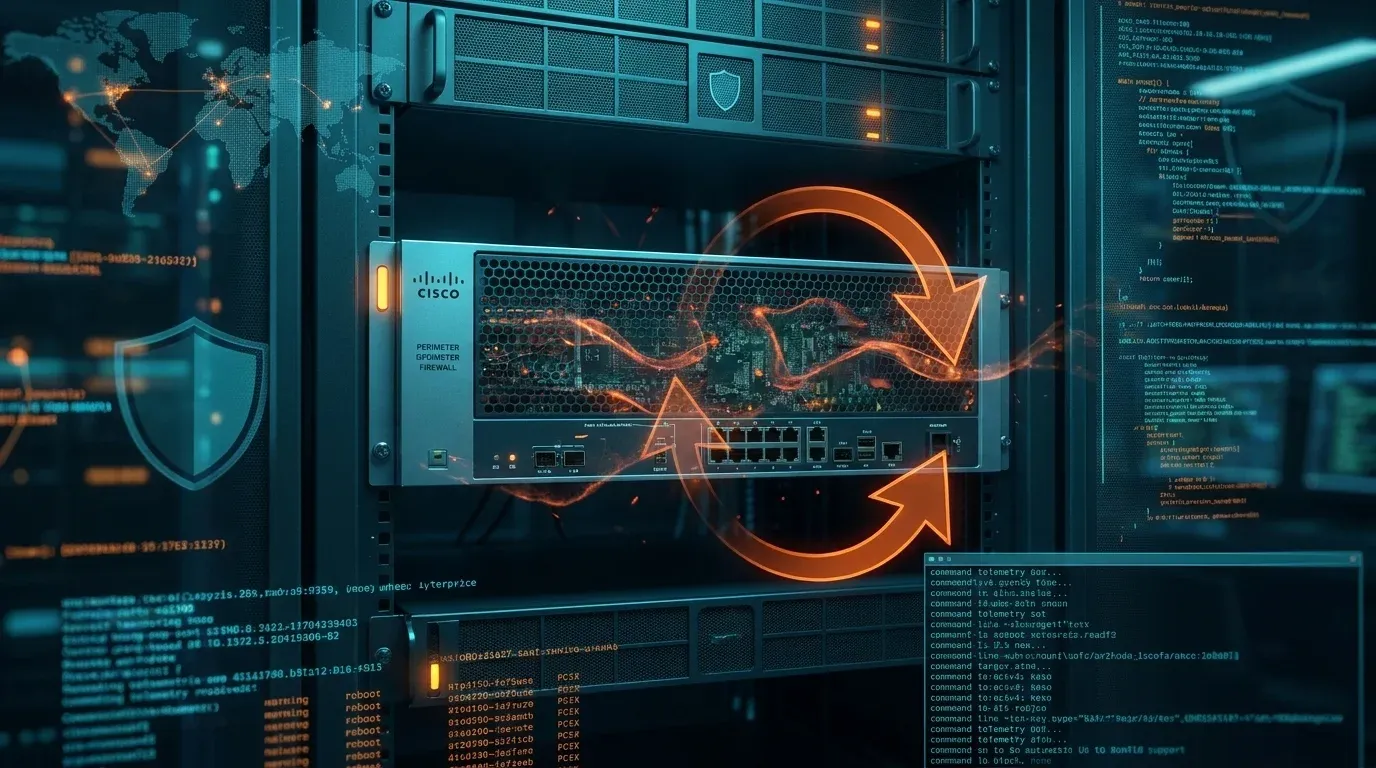
Firestarter leaves patched Cisco firewalls at continued risk
Firestarter leaves patched Cisco firewalls at continued risk A newly detailed persistence mechanism called Firestarter changes the defender story around last ye...
Lucas Oliveira
Research
AgingFly campaign hits Ukrainian government and hospital networks
AgingFly campaign hits Ukrainian government and hospital networks A newly reported campaign centered on the AgingFly backdoor is a reminder that targeted intrus...
Lucas Oliveira
Research
CPUID breach turned CPU-Z and HWMonitor into a malware delivery path
CPUID breach turned CPU-Z and HWMonitor into a malware delivery path Executive summary A compromise of the CPUID website briefly turned trusted download links f...
Lucas Oliveira
Research
Axios npm compromise pushed a cross-platform RAT through a fake dependency
Axios npm compromise pushed a cross-platform RAT through a fake dependency A compromise of the widely used axios package on npm shows why defenders cannot rely...
Lucas Oliveira
Research
Trivy GitHub Action compromise exposed CI/CD secrets in a stealth supply-chain attack
Trivy GitHub Action compromise exposed CI/CD secrets in a stealth supply-chain attack A supply-chain compromise in Aqua Security’s aquasecurity/trivy-action sho...
Lucas Oliveira
Research
GlassWorm Shifts to Transitive Open VSX Dependencies in Developer Supply-Chain Push
GlassWorm Shifts to Transitive Open VSX Dependencies in Developer Supply-Chain Push GlassWorm is no longer just a story about obviously malicious extensions. Th...
Lucas Oliveira
Research
Slopoly Shows How AI-Generated Malware Is Entering Ransomware Operations
Slopoly Shows How AI-Generated Malware Is Entering Ransomware Operations | 2026 Executive Summary IBM X-Force says a ransomware-linked intrusion involved a like...
Lucas Oliveira
Research