Executive Summary
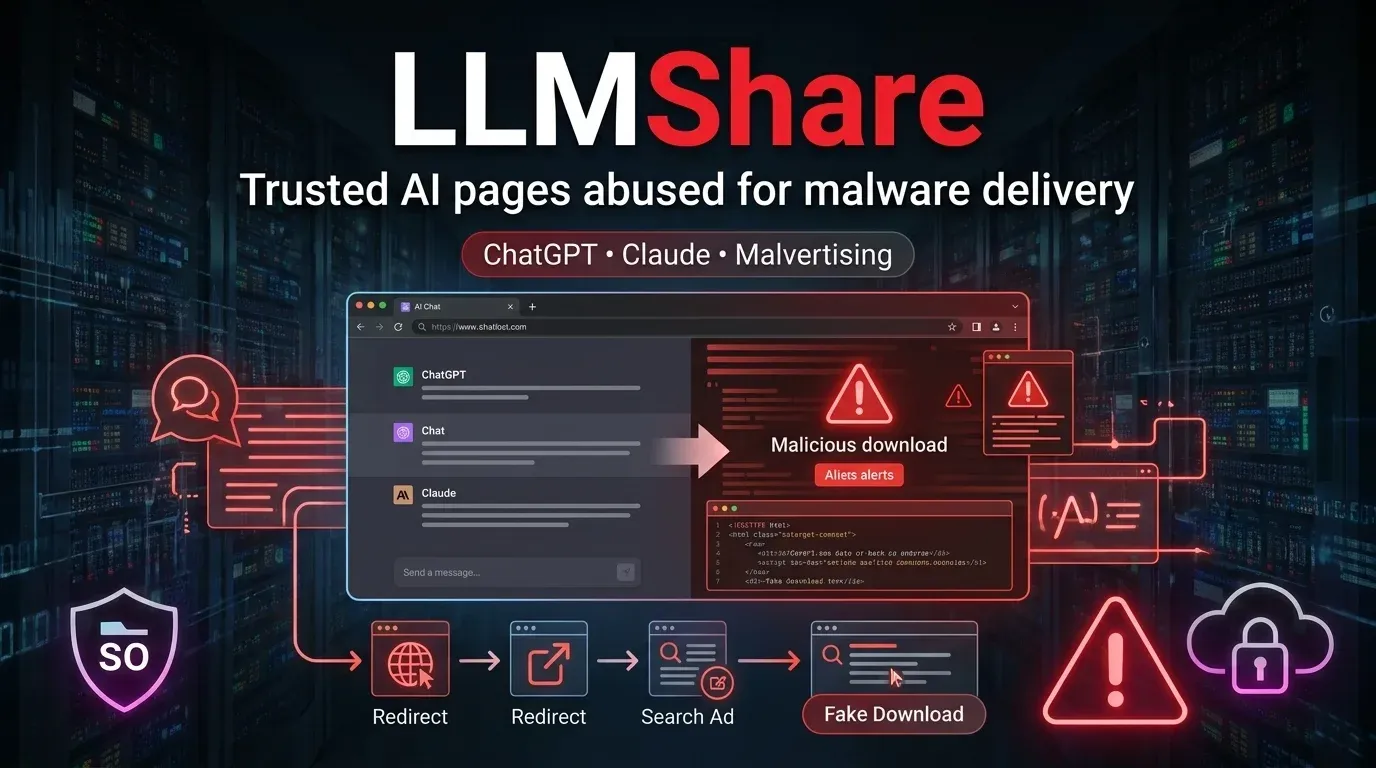
IBM X-Force says a ransomware-linked intrusion involved a likely AI-generated malware component dubbed Slopoly, used by a threat cluster tracked as Hive0163. The malware itself is not especially sophisticated, but that is exactly why the case matters. It shows how threat actors can use AI to rapidly build workable persistence and command-and-control tooling without needing elite malware engineering skills.
For defenders, the lesson is not that Slopoly is a breakthrough implant. It is that AI lowers the cost and time required to create custom malware, test variants, and extend intrusion chains during live ransomware operations.
What happened
According to IBM X-Force, Hive0163 used Slopoly during a ransomware attack after initial access was obtained through a ClickFix social engineering chain. The victim was manipulated into executing a malicious PowerShell command, which led to deployment of the group's broader malware stack, including NodeSnake, InterlockRAT, and later Slopoly.
IBM describes Slopoly as a PowerShell-based client for a novel command-and-control framework. The script appears to have been generated with LLM assistance and deployed on an infected server to maintain persistence for more than a week during the later stages of the intrusion.
Why this matters
1. The barrier to malware development keeps dropping
Slopoly does not need to be technically brilliant to be operationally useful. AI-generated malware can still help threat actors produce bespoke tooling faster, adjust code during intrusions, and reduce dependence on experienced developers.
2. "Good enough" malware is enough for real intrusions
IBM's assessment is that the code quality was mediocre and overstated its own capabilities. Even so, it worked. It beaconed to a C2 server, executed commands via cmd.exe, maintained logs, and helped the attackers stay on the compromised server.
3. AI is becoming part of ransomware tradecraft
The bigger issue is not one script. It is the direction of travel. IBM and other incident responders are seeing signs that criminal groups are starting to use AI to support malware development, operational testing, and attack execution inside real ransomware campaigns.
Technical takeaways
IBM says Slopoly collected basic host data and sent JSON heartbeats to its C2 endpoint. It reportedly beaconed every 30 seconds, polled for commands every 50 seconds, and executed received tasks through cmd.exe. Persistence was established through a scheduled task named Runtime Broker under a path in C:\ProgramData\Microsoft\Windows\Runtime\.
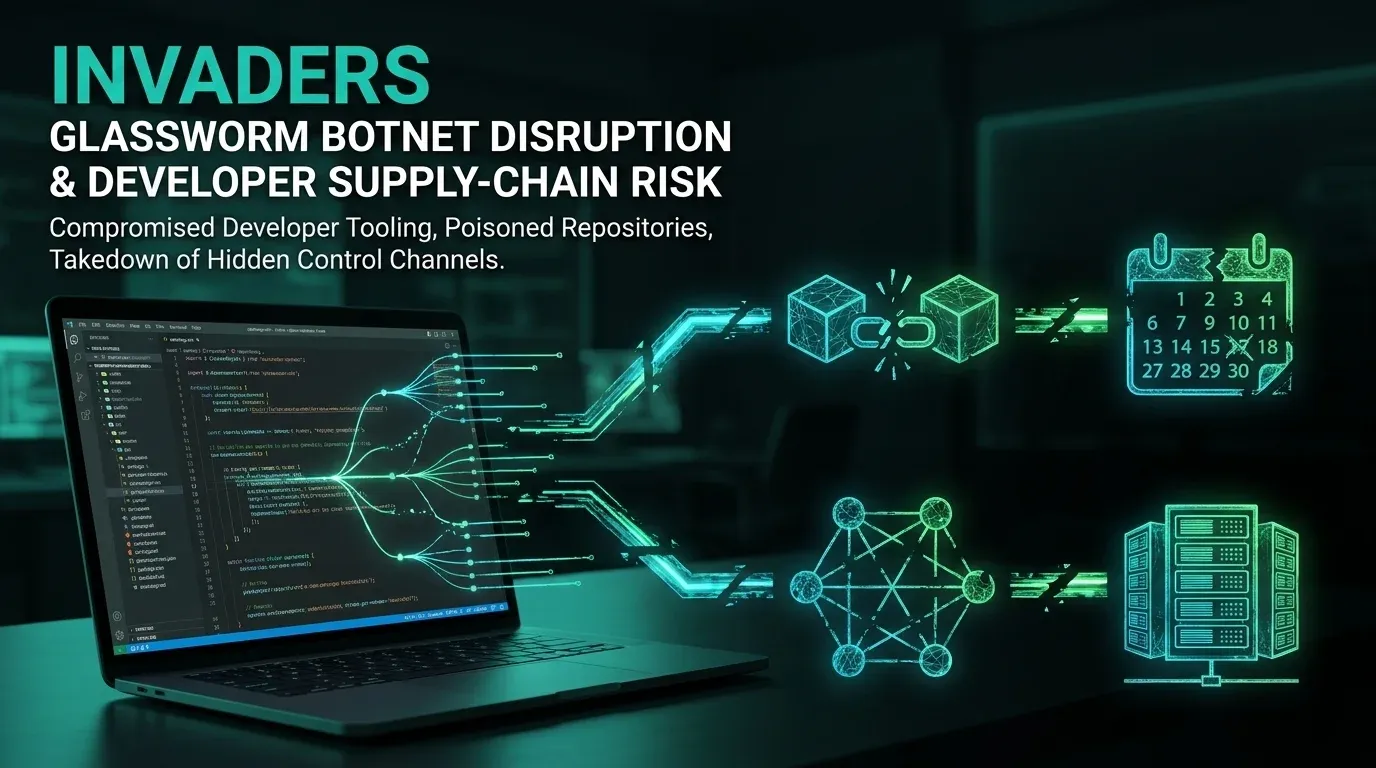
The intrusion chain also included:
- ClickFix for initial user execution
- NodeSnake as an early-stage implant
- InterlockRAT for more capable access, including SOCKS5 tunneling and reverse shell features
- common follow-on tooling such as AzCopy and Advanced IP Scanner
This combination matters because Slopoly was not acting alone. It was one component in a post-compromise ecosystem built for persistence, movement, and data theft ahead of ransomware deployment.
Immediate actions for defenders
🔴 Hunt for ClickFix-style execution chains
Review telemetry for suspicious use of Win+R, clipboard-triggered PowerShell execution, unusual child processes, and scripted execution launched from fake verification or CAPTCHA-style pages.
🔴 Watch for persistence and post-compromise staging
Look for suspicious scheduled tasks such as Runtime Broker, PowerShell artifacts under unusual Windows-looking paths, rapid beaconing to unfamiliar HTTP endpoints, and command execution via cmd.exe from scripted implants.
🔴 Prioritize detection of data theft enablers
If Hive0163-style activity is in scope, watch for AzCopy, Advanced IP Scanner, web-socket based backdoors, SOCKS tunneling, reverse shells, and connections to unexpected Cloudflare tunnel domains.
🟠 Update your threat model for AI-assisted malware
Do not wait for "advanced" AI implants to appear before adjusting detections. Lower-quality but quickly generated malware can still extend dwell time, persistence, and operator flexibility during ransomware intrusions.
Strategic takeaway
Slopoly is a warning sign more than a technical marvel. AI-generated malware does not need to be elegant to change defender economics. If threat actors can produce new backdoors faster, adapt them mid-intrusion, and use them as disposable tooling in ransomware operations, incident response teams will face more frequent and more customized malware variants.
That means defenders should focus less on whether a sample looks impressive and more on whether it helps attackers move faster. In that respect, Slopoly already matters.
Is Slopoly a sophisticated malware family?
Not really. IBM X-Force describes it as functional but technically mediocre. The significance is that it appears to be AI-generated and still proved useful in a real ransomware intrusion.
Which group used Slopoly?
IBM attributes the activity to a financially motivated cluster tracked as Hive0163, associated with large-scale data exfiltration and ransomware operations.
What was the initial access method?
IBM says the intrusion began with a ClickFix social engineering attack that tricked the victim into running a malicious PowerShell command.
References
- IBM X-Force - A Slopoly start to AI-enhanced ransomware attacks
- Palo Alto Unit 42 - 2026 Global Incident Response Report
- Proofpoint - ClickFix social engineering technique floods threat landscape
Published: 2026-03-17 Author: Invaders Cybersecurity Classification: Public / TLP:CLEAR Reading Time: 5 minutes