#Threat Intel
Palo Alto GlobalProtect auth bypass turns cookie trust into VPN access risk
Palo Alto GlobalProtect auth bypass turns cookie trust into VPN access risk CVE-2026-0257 matters because it turns a trust shortcut on the VPN edge into an iden...
Lucas Oliveira
Research
FortiClient EMS exploit turns endpoint management into credential theft at scale
FortiClient EMS exploit turns endpoint management into credential theft at scale CVE-2026-35616 matters because it breaks a security assumption many teams quiet...
Lucas Oliveira
Research
GlassWorm takedown shows how developer malware becomes supply-chain risk
GlassWorm takedown shows how developer malware becomes supply-chain risk Executive Summary The coordinated disruption of GlassWorm on May 26, 2026 is useful bec...
Lucas Oliveira
Research
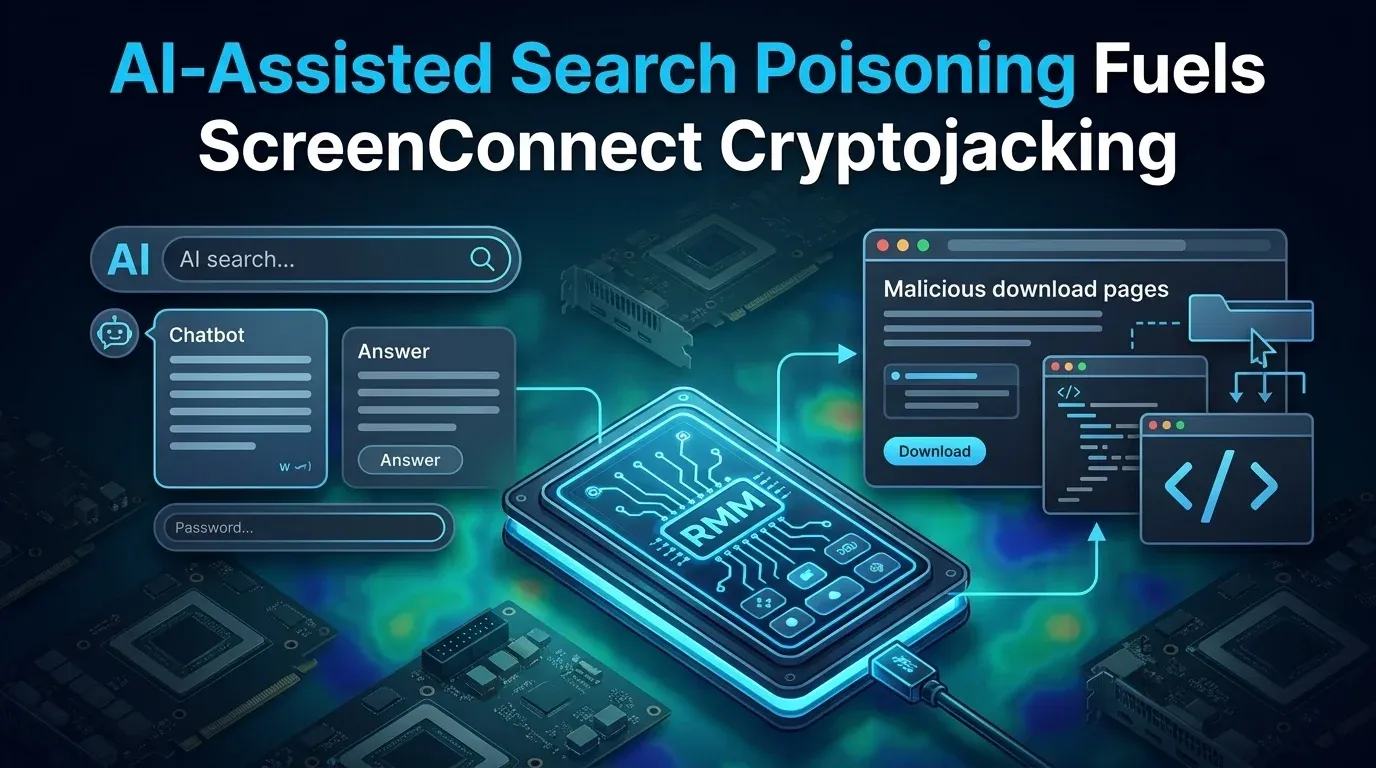
AI-Assisted Search Poisoning Fuels ScreenConnect Cryptojacking
AI-Assisted Search Poisoning Fuels ScreenConnect Cryptojacking Executive Summary Microsoft disclosed an active campaign on May 26, 2026 in which attackers push...
Lucas Oliveira
Research
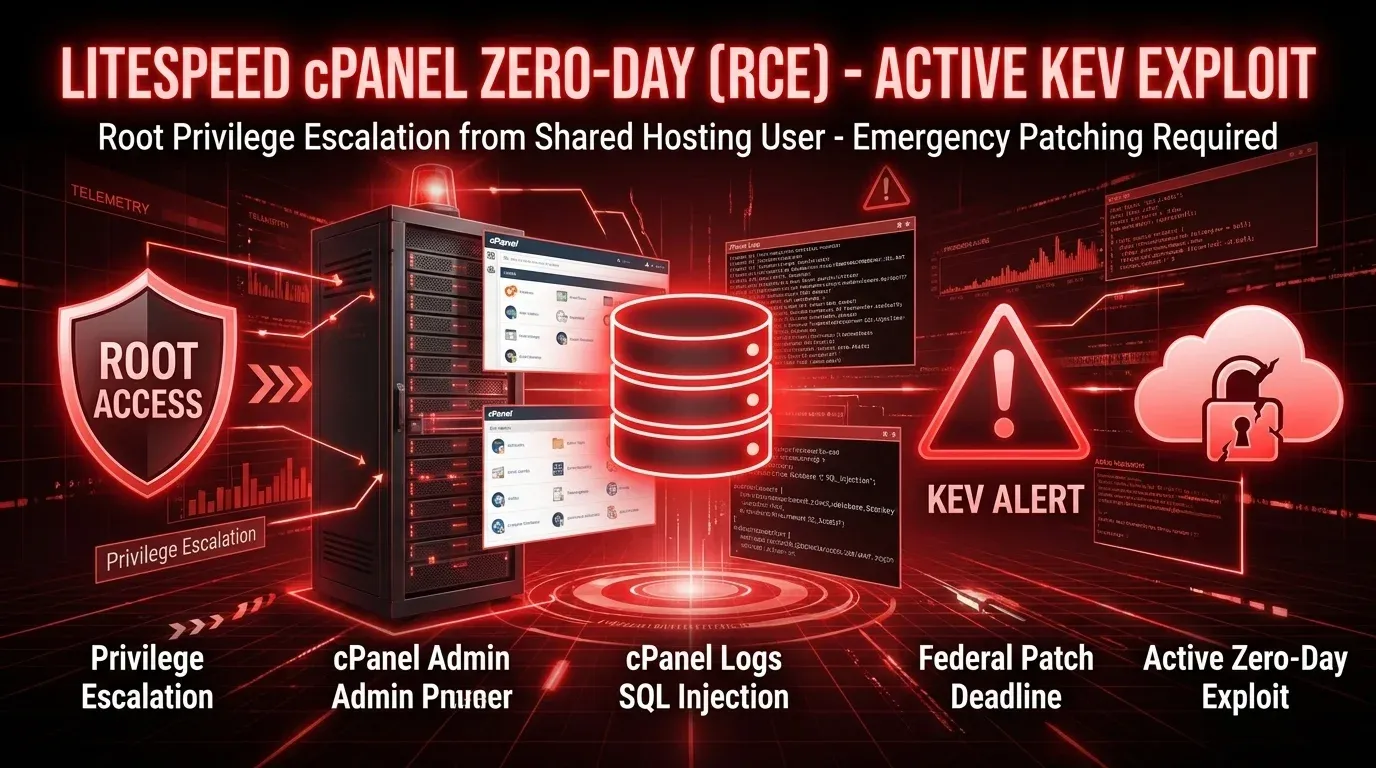
CVE-2026-48172 puts LiteSpeed cPanel deployments on a KEV deadline
CVE-2026-48172 puts LiteSpeed cPanel deployments on a KEV deadline CVE-2026-48172 has escalated from vendor emergency to federal patching priority. On May 26, 2...
Lucas Oliveira
Research
Kazuar’s redesign turns a familiar backdoor into a harder-to-hunt botnet
Kazuar’s redesign turns a familiar backdoor into a harder-to-hunt botnet Microsoft’s latest research on Kazuar matters because it reframes the malware from a we...
Lucas Oliveira
Research
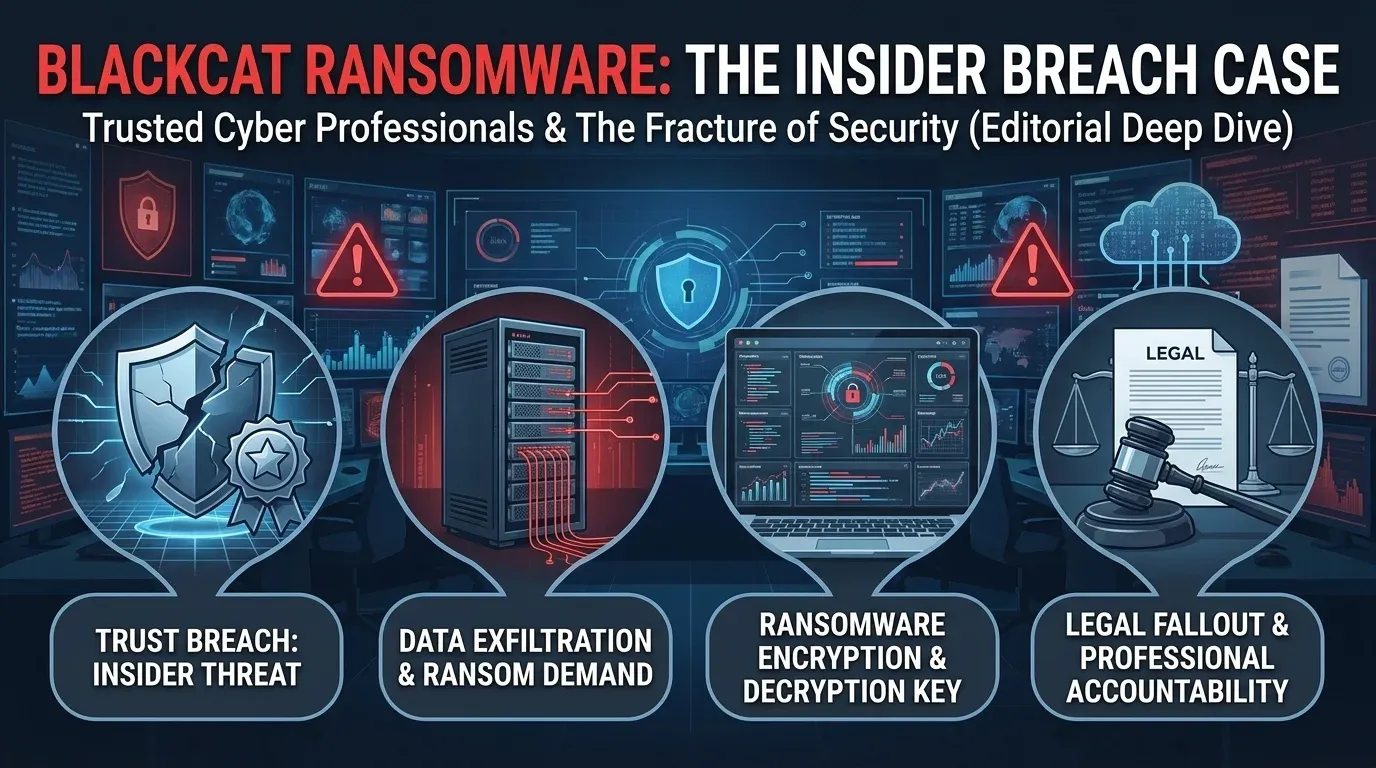
BlackCat case shows ransomware risk inside trusted cyber roles
BlackCat case shows ransomware risk inside trusted cyber roles A new U.S. criminal case tied to BlackCat (ALPHV) is a sharp reminder that ransomware risk is not...
Lucas Oliveira
Research
PyTorch Lightning supply-chain compromise puts AI developer credentials at risk
PyTorch Lightning supply-chain compromise puts AI developer credentials at risk The most dangerous supply-chain incidents are not always the ones that hit opera...
Lucas Oliveira
Research
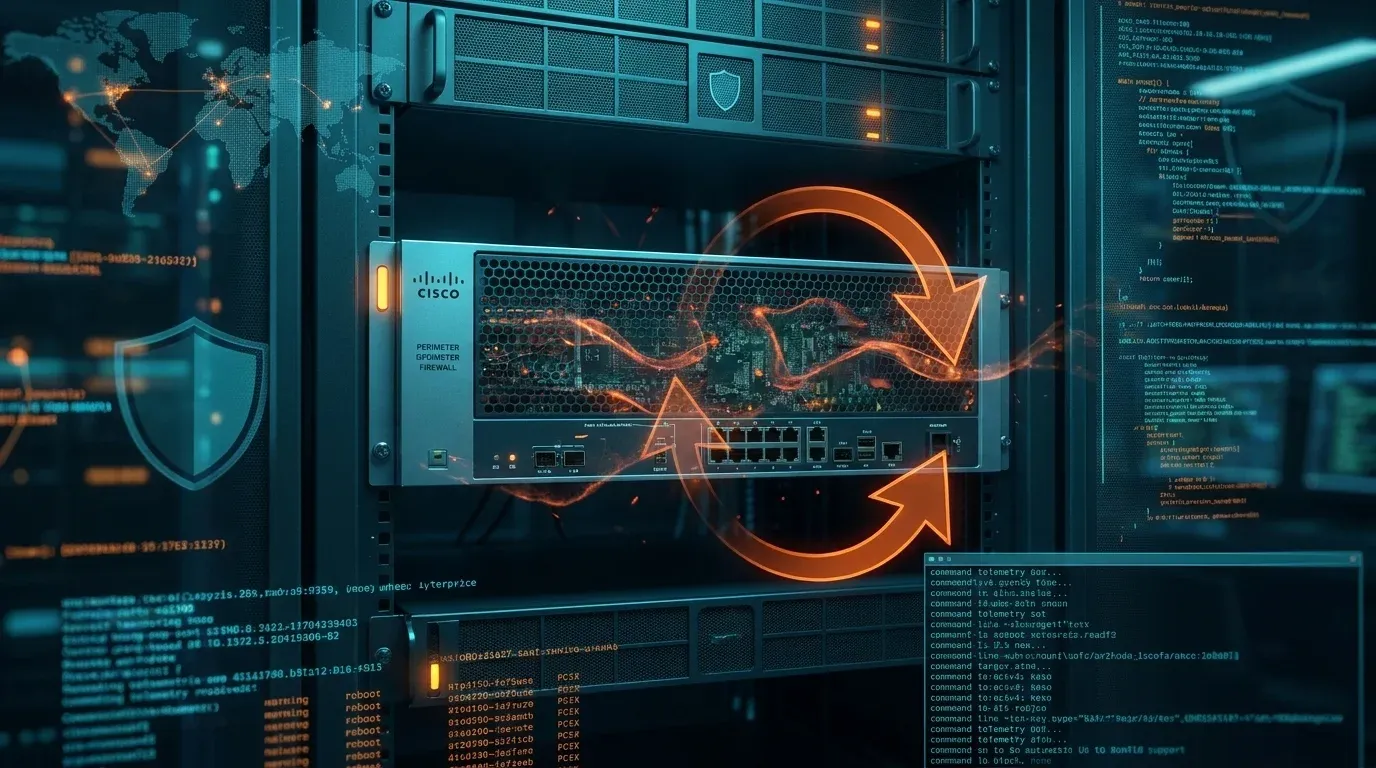
Firestarter leaves patched Cisco firewalls at continued risk
Firestarter leaves patched Cisco firewalls at continued risk A newly detailed persistence mechanism called Firestarter changes the defender story around last ye...
Lucas Oliveira
Research
AgingFly campaign hits Ukrainian government and hospital networks
AgingFly campaign hits Ukrainian government and hospital networks A newly reported campaign centered on the AgingFly backdoor is a reminder that targeted intrus...
Lucas Oliveira
Research
Iranian PLC Attacks Disrupt U.S. Critical Infrastructure
Iranian PLC Attacks Disrupt U.S. Critical Infrastructure Executive Summary Iranian-affiliated [advanced persistent threat](https://invaders.ie/resources/glossar...
Lucas Oliveira
Research
Trivy GitHub Action compromise exposed CI/CD secrets in a stealth supply-chain attack
Trivy GitHub Action compromise exposed CI/CD secrets in a stealth supply-chain attack A supply-chain compromise in Aqua Security’s aquasecurity/trivy-action sho...
Lucas Oliveira
Research