#Privilege Escalation
CVE-2026-48172 puts LiteSpeed cPanel deployments on a KEV deadline
CVE-2026-48172 puts LiteSpeed cPanel deployments on a KEV deadline CVE-2026-48172 has escalated from vendor emergency to federal patching priority. On May 26, 2...
Lucas Oliveira
Research
Dirty Frag Linux kernel zero-day gives local users a fast path to root
Dirty Frag Linux kernel zero-day gives local users a fast path to root Dirty Frag is the kind of Linux bug defenders worry about because it turns a limited foot...
Lucas Oliveira
Research
Dirty Frag Linux kernel zero-day gives local users a fast path to root
Dirty Frag Linux kernel zero-day gives local users a fast path to root Dirty Frag deserves attention because it is not a theoretical Linux bug waiting for slow...
Lucas Oliveira
Research
CVE-2026-31431: Copy Fail turns routine Linux access into reliable root compromise
CVE-2026-31431: Copy Fail turns routine Linux access into reliable root compromise Copy Fail is the kind of Linux flaw defenders should not shrug off just becau...
Lucas Oliveira
Research
Pack2TheRoot flaw puts Linux systems with PackageKit on a local root path
Pack2TheRoot flaw puts Linux systems with PackageKit on a local root path The newly disclosed Pack2TheRoot issue, tracked as CVE-2026-41651, is a strong reminde...
Lucas Oliveira
Research
Leaked Windows Defender zero-days are already being used to gain SYSTEM access
Leaked Windows Defender zero-days are already being used to gain SYSTEM access A fast-moving Windows story matters to defenders this week for a simple reason: p...
Lucas Oliveira
Research
CVE-2026-34040 puts Docker image-mount trust on the host-root risk path
CVE-2026-34040 puts Docker image-mount trust on the host-root risk path CVE-2026-34040 is the kind of Docker bug that changes the conversation from ordinary con...
Lucas Oliveira
Research
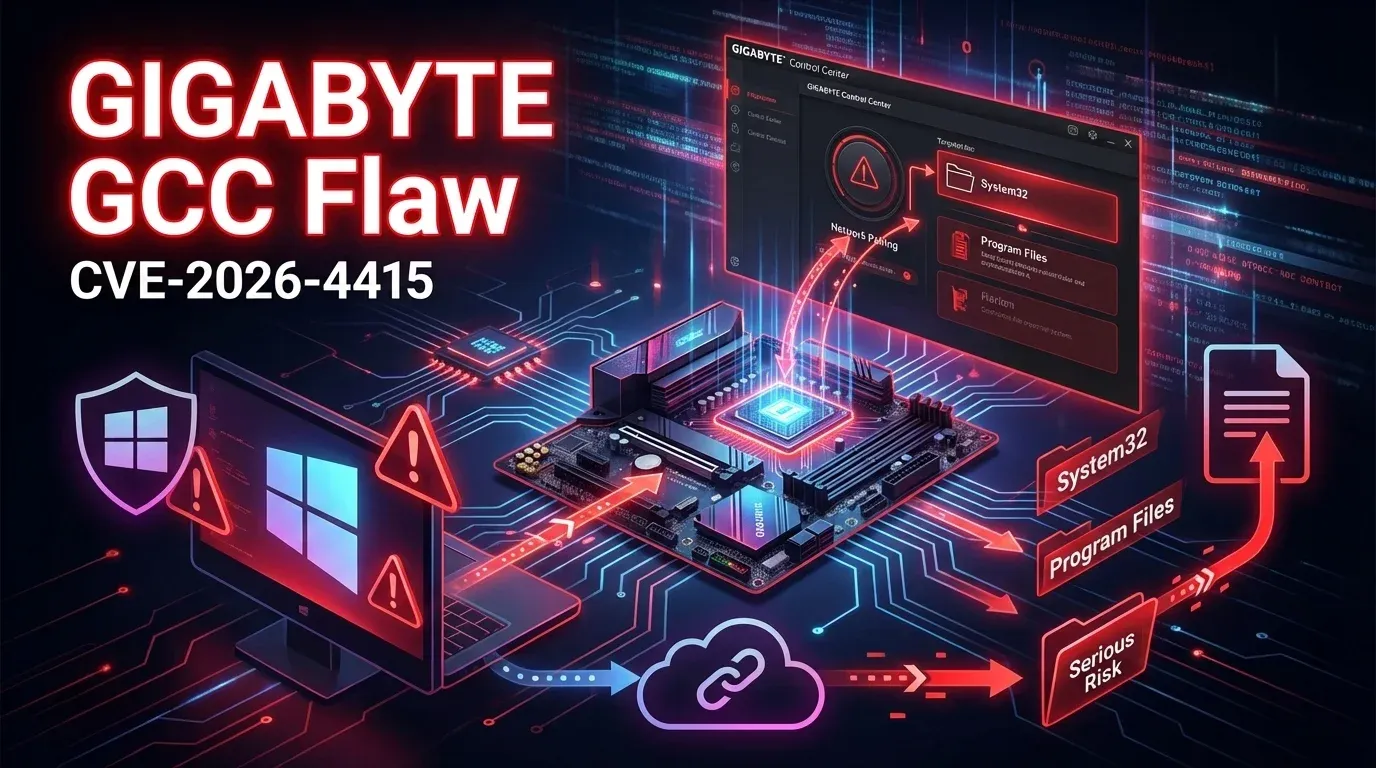
GIGABYTE Control Center flaw turns a convenience utility into a remote compromise path
GIGABYTE Control Center flaw turns a convenience utility into a remote compromise path Security teams often focus on browsers, VPNs, and internet-facing servers...
Lucas Oliveira
Research