#Threat Intelligence
DAEMON Tools supply-chain attack turns trusted installers into a malware delivery path
DAEMON Tools supply-chain attack turns trusted installers into a malware delivery path The most important part of the DAEMON Tools incident is not that malware...
Lucas Oliveira
Research
Vishing and SSO abuse are accelerating rapid SaaS extortion
Vishing and SSO abuse are accelerating rapid SaaS extortion The most dangerous part of modern SaaS intrusions is not always malware. Sometimes it is speed, trus...
Lucas Oliveira
Research
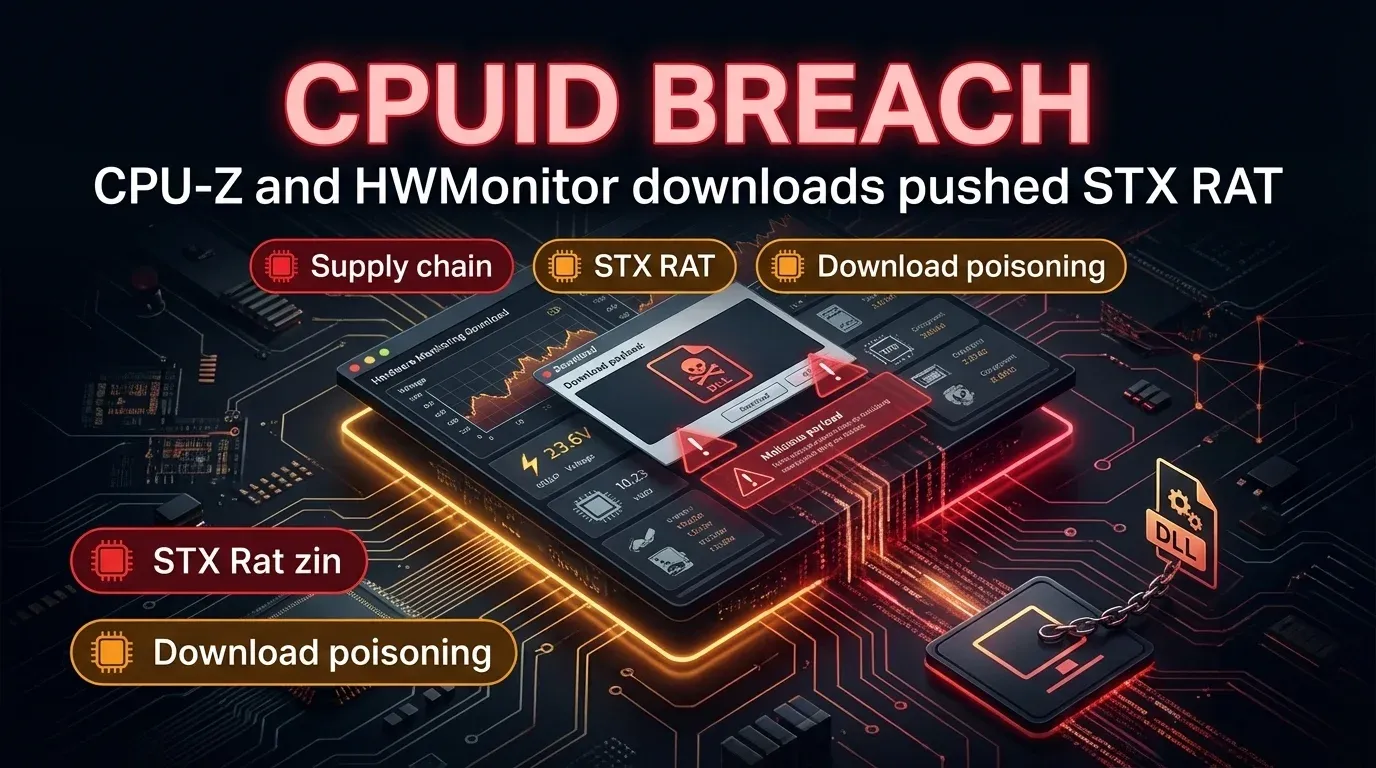
CPUID breach turned CPU-Z and HWMonitor into a malware delivery path
CPUID breach turned CPU-Z and HWMonitor into a malware delivery path Executive summary A compromise of the CPUID website briefly turned trusted download links f...
Lucas Oliveira
Research
Storm-1175 turns patch gaps into rapid Medusa ransomware intrusions
Storm-1175 turns patch gaps into rapid Medusa ransomware intrusions Storm-1175 is a financially motivated threat actor that Microsoft says has been using newly...
Lucas Oliveira
Research
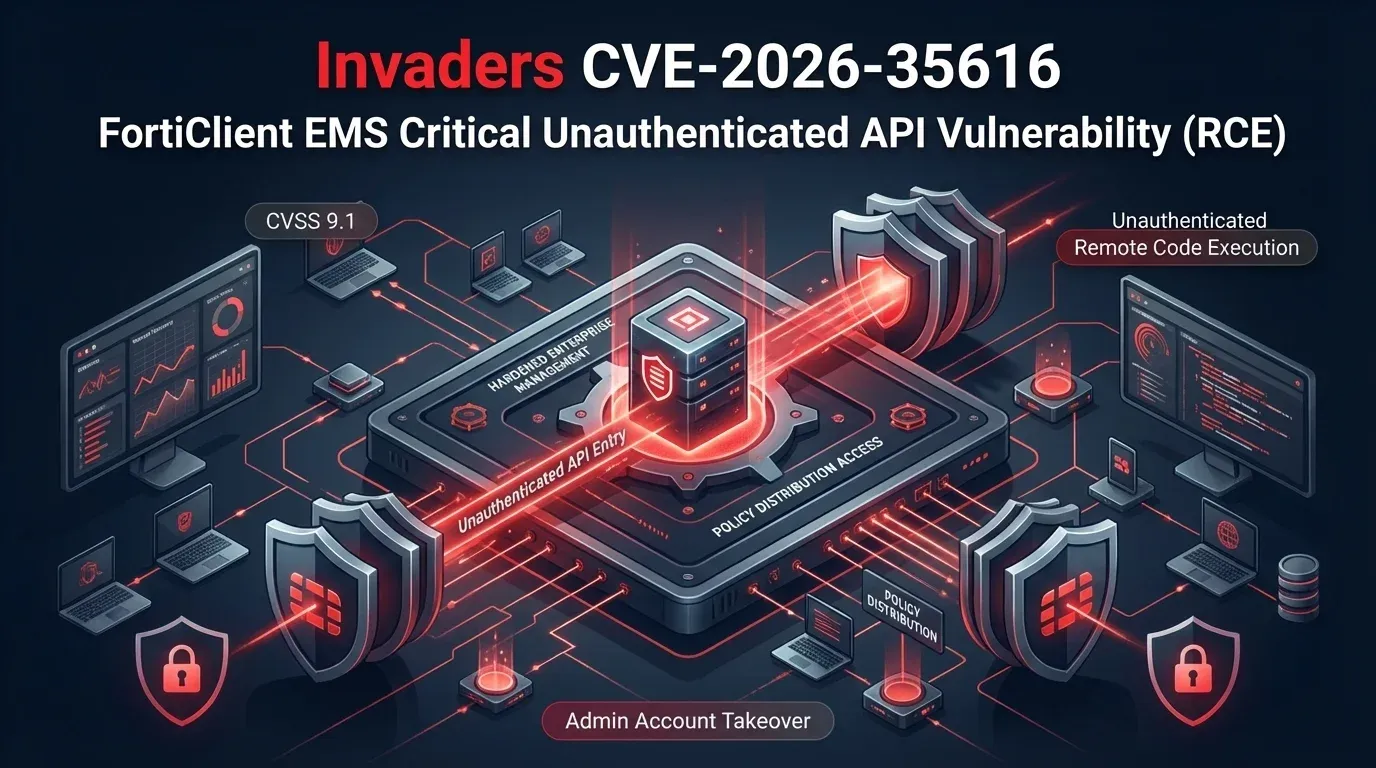
CVE-2026-35616 puts exposed FortiClient EMS servers into the incident-response lane
CVE-2026-35616 puts exposed FortiClient EMS servers into the incident-response lane CVE-2026-35616 is the second serious FortiClient EMS story in less than two...
Lucas Oliveira
Research
European Commission breach shows how stolen cloud secrets can spill across shared public platforms
European Commission breach shows how stolen cloud secrets can spill across shared public platforms The latest details on the European Commission cloud incident...
Lucas Oliveira
Research
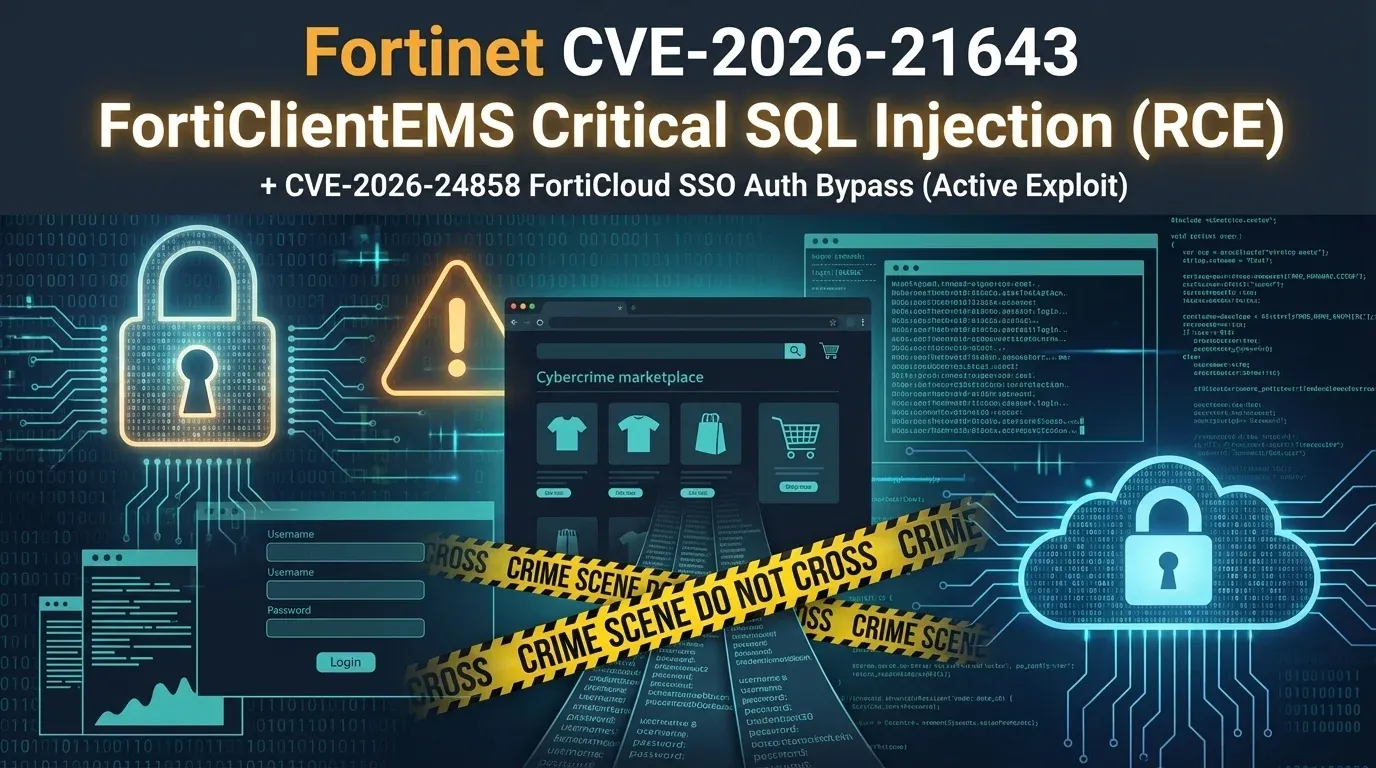
CVE-2026-21643: FortiClient EMS exploitation puts exposed endpoint managers at immediate risk
CVE-2026-21643: FortiClient EMS exploitation puts exposed endpoint managers at immediate risk CVE-2026-21643 is the kind of flaw defenders should treat as an im...
Lucas Oliveira
Research
LeakBase arrest is a warning to review stolen credential exposure now
LeakBase arrest is a warning to review stolen credential exposure now | 2026 The reported arrest of the alleged LeakBase administrator in Russia is the kind of...
Lucas Oliveira
Research
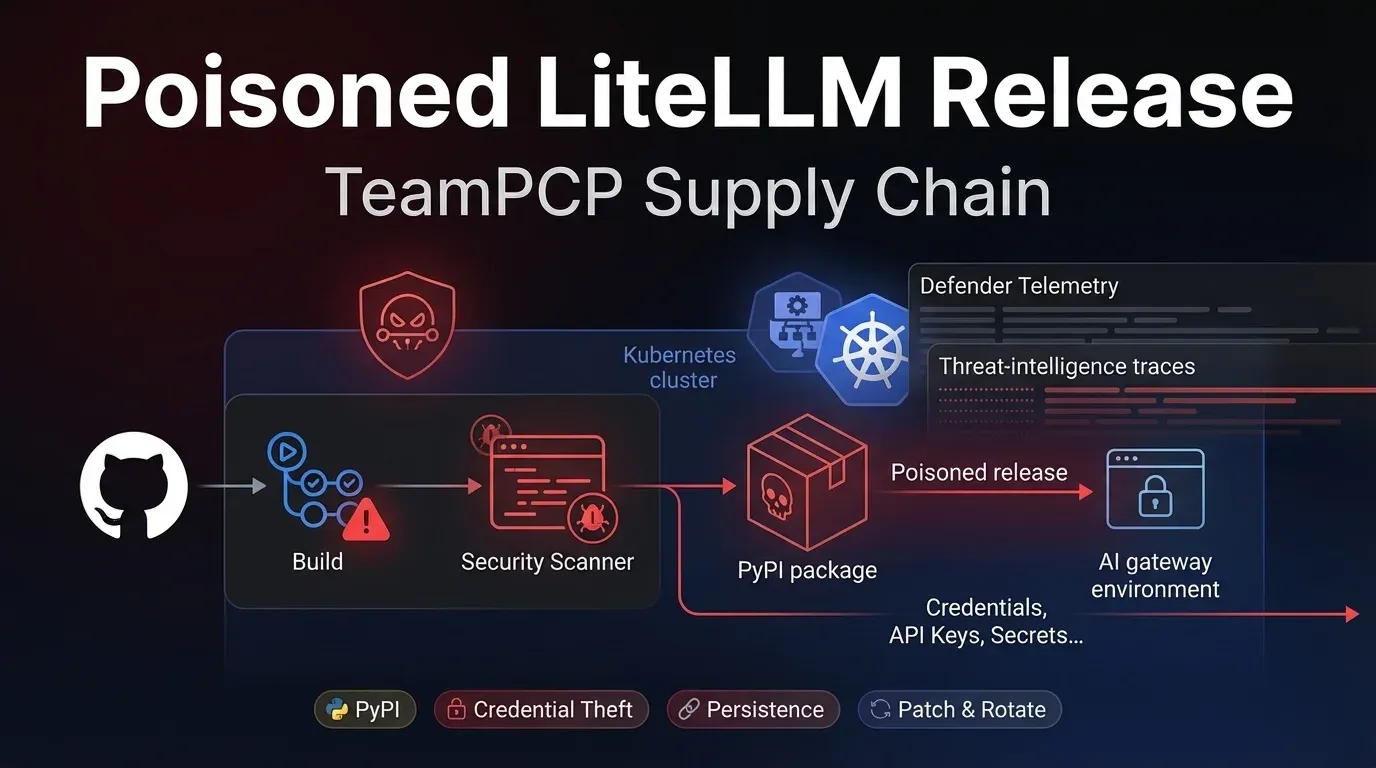
Poisoned Trivy scanner led to malicious LiteLLM releases on PyPI
Poisoned Trivy scanner led to malicious LiteLLM releases on PyPI | 2026 The LiteLLM incident is what modern software supply-chain compromise looks like when one...
Lucas Oliveira
Research
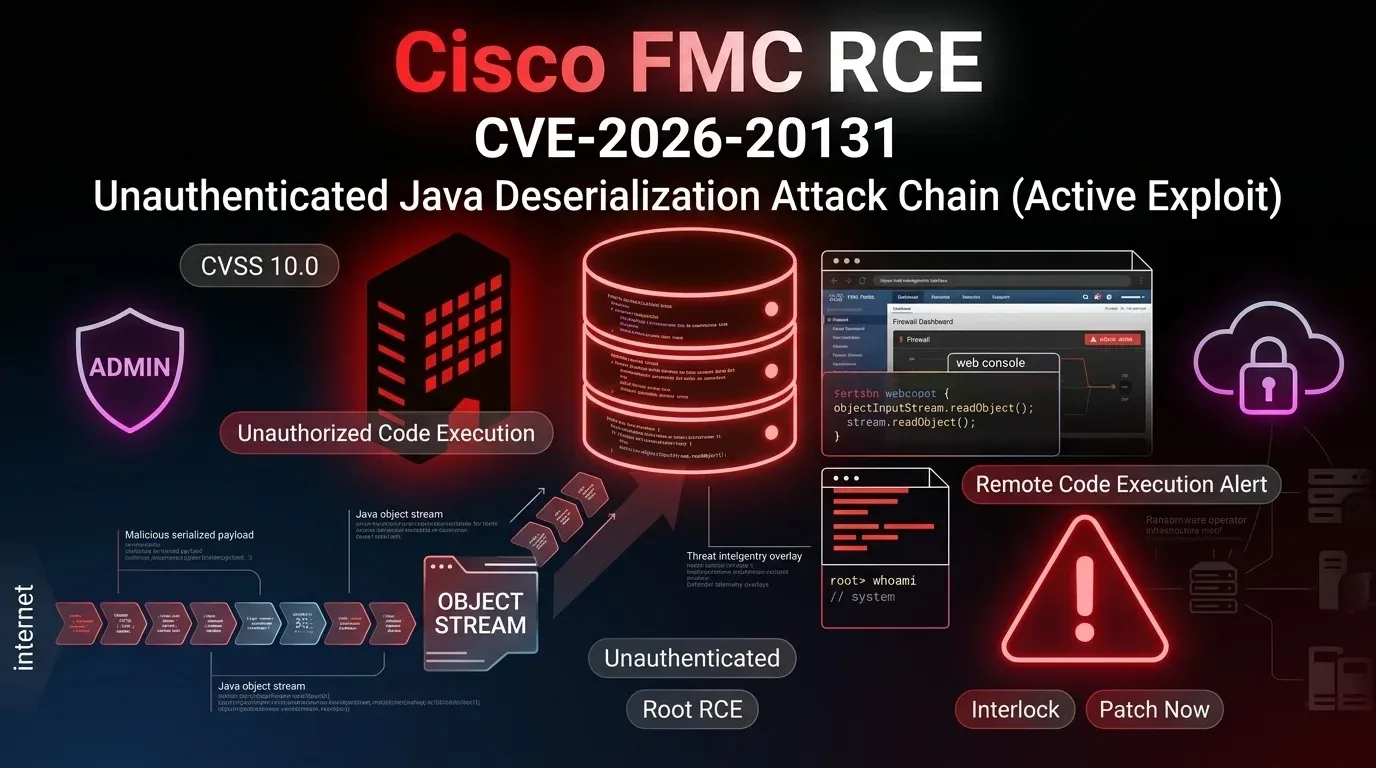
CVE-2026-20131: Interlock hit Cisco FMC before disclosure
CVE-2026-20131: Interlock hit Cisco FMC before disclosure | 2026 CVE-2026-20131 is the kind of firewall-management flaw defenders dread: an unauthenticated bug...
Lucas Oliveira
Research
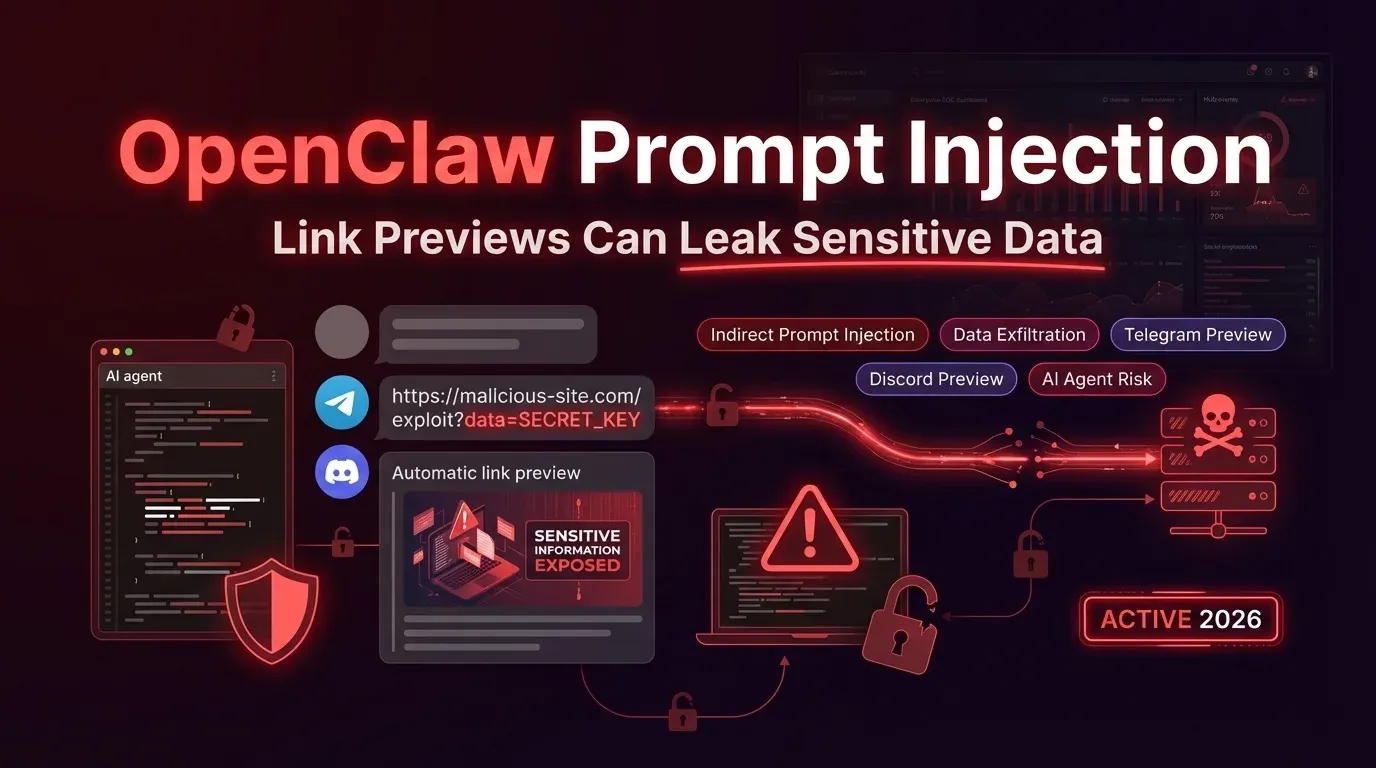
OpenClaw AI Agents Can Leak Data via Indirect Prompt Injection
OpenClaw AI Agents Can Leak Data via Indirect Prompt Injection | 2026 Executive Summary OpenClaw is facing renewed scrutiny after reporting from The Hacker News...
Lucas Oliveira
Research
CVE-2025-26399: SolarWinds WHD Exploitation Hits Servers
CVE-2025-26399: SolarWinds WHD Exploitation Hits Servers | 2026 Executive Summary CVE-2025-26399 in SolarWinds Web Help Desk has moved from “critical but patcha...
Lucas Oliveira
Research