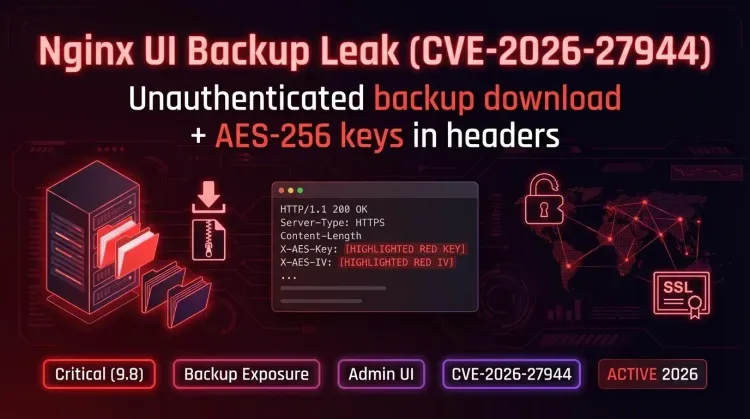
A critical vulnerability has been reported in Nginx UI, tracked as CVE-2026-27944 (CVSS 9.8). The flaw allows unauthenticated attackers to download full server backups and exposes the parameters required to decrypt them.
What happens
- The /api/backup endpoint does not require authentication, allowing anyone to request a full system backup.
- The HTTP response includes the AES-256 encryption key and IV in the X-Backup-Security header, enabling an attacker to decrypt the archive immediately.
Impact
Exploitation can lead to exposure of administrative credentials, session tokens, private SSL keys, and configuration files — enabling takeover of the management interface and potential man-in-the-middle attacks.
Immediate mitigations
- Isolate the Nginx UI: remove public exposure of the management panel — place it behind a VPN or private network.
- Implement strong authentication and MFA for the management panel.
- Block or remove access to the /api/backup endpoint until a fix is available.
- Rotate any keys/credentials that may have been included in backups.
- Audit access logs for unauthorized backup downloads.
Conclusion
CVE-2026-27944 shows how poorly protected administrative interfaces can create high-impact risks. Prioritize isolating the panel, blocking sensitive endpoints, and rotating compromised keys as needed.