Executive Summary
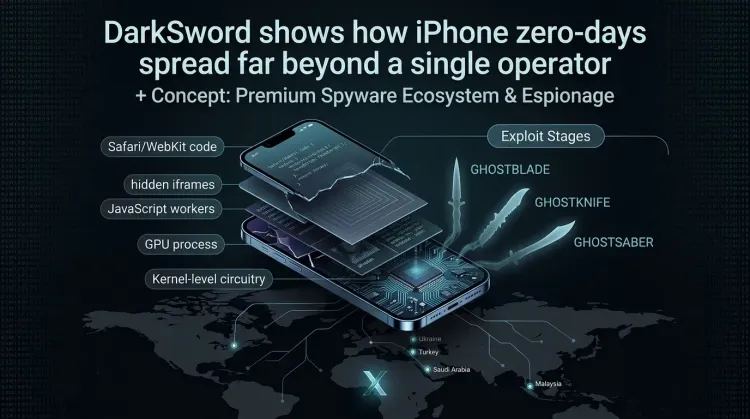
Google Threat Intelligence Group says DarkSword is a full-chain iOS exploit that used six vulnerabilities to fully compromise iPhones running iOS 18.4 through 18.7. The more important story is not just the exploit chain itself. It is the way DarkSword spread across different operators: UNC6748 in Saudi Arabia, PARS Defense activity in Turkey and Malaysia, and UNC6353, a suspected Russian espionage actor, in watering-hole attacks against Ukrainian users.
That is the part defenders should focus on. A premium mobile zero-day capability did not stay exclusive. It moved across commercial surveillance operations and state-linked espionage, with different payloads, different operational tradecraft, and the same core exploitation path underneath.
What happened?
According to Google, DarkSword has been active since at least November 2025. Across the observed campaigns, the chain delivered three different JavaScript malware families after compromise:
- GHOSTKNIFE used by UNC6748
- GHOSTSABER used in PARS Defense-linked activity
- GHOSTBLADE used by UNC6353
The campaigns were geographically distinct, but technically related:
- Saudi Arabia: UNC6748 used a Snapchat-themed lure site,
snapshare[.]chat, to deliver DarkSword. - Turkey and Malaysia: Google linked separate DarkSword activity to PARS Defense customers.
- Ukraine: UNC6353 used compromised Ukrainian websites as watering holes and delivered DarkSword from
static.cdncounter[.]net.
Google reported the vulnerabilities to Apple in late 2025. GTIG says all of the vulnerabilities used by DarkSword were patched by iOS 26.3, although most of them were fixed earlier in the iOS 18.7.x and 26.x branches.
Why this matters
1. DarkSword is a proliferation story
This is not just another mobile bug report. It is evidence that advanced iPhone exploitation keeps moving between vendors, customers, and state-linked operators. That kind of capability reuse compresses the gap between boutique spyware activity and mainstream high-end intrusion operations.
2. The chain was mature enough to support multiple payloads
DarkSword was not tied to one implant. Google found the same exploitation framework leading to different post-exploitation outcomes:
- GHOSTKNIFE acted as a backdoor with data theft, screenshots, audio recording, and file download features.
- GHOSTSABER focused on device enumeration, exfiltration, and arbitrary JavaScript execution.
- GHOSTBLADE behaved more like a dataminer, harvesting messages, Wi-Fi data, keychain-related information, photos metadata, notes, calendars, and cryptocurrency wallet data.
That flexibility matters because defenders cannot assume one exploit chain maps neatly to one malware family or one actor profile.
3. Mobile exploitation is not a niche problem
UNC6353’s use of DarkSword against Ukrainian targets is the clearest reminder here. High-end iPhone exploitation is part of real-world espionage tradecraft, not just a premium surveillance market curiosity. Security teams that still treat mobile compromise as edge-case risk are behind the curve.
How the exploit chain worked
Google says DarkSword used six vulnerabilities to move from Safari-based remote code execution to full kernel privileges.
Remote code execution
DarkSword used different JavaScriptCore bugs depending on the iOS version:
- CVE-2025-31277 for versions before iOS 18.6
- CVE-2025-43529 for iOS 18.6 through 18.7
Both were chained with CVE-2026-20700, a dyld Pointer Authentication Code bypass that helped the attackers execute arbitrary code and continue the chain.
Sandbox escape
After initial execution, DarkSword escaped Safari’s sandbox in two steps:
- CVE-2025-14174 in ANGLE to pivot from WebContent into the GPU process.
- CVE-2025-43510 in XNU to pivot again into
mediaplaybackd, a more privileged system service.
Privilege escalation
The final step used CVE-2025-43520, a kernel race condition in XNU’s VFS layer, to gain full kernel privileges and deploy the final payload.
What made the delivery tradecraft interesting
The delivery side was not identical across operators, but Google says the overlap is strong enough to suggest a shared developer base behind DarkSword.
Common themes included:
- hidden iframes and staged JavaScript loaders
- use of a
uidsession storage key to manage infection logic - Safari-focused delivery paths
- version-aware exploit workers for different iOS builds
There were also clear operator-level differences:
- UNC6748 used a Snapchat-themed decoy and even pushed Chrome users toward Safari with the
x-safari-httpshandler. - PARS Defense added stronger OPSEC, including encrypted exploit delivery with ECDH and AES, plus extra device fingerprinting.
- UNC6353 delivered DarkSword through compromised Ukrainian sites and used a simpler watering-hole implementation that still correctly handled iOS version selection.
What defenders should do now
Immediate actions
- identify users who may still have devices on older iOS 18.4 to 18.7-era builds or who were slow to apply subsequent fixes
- prioritize high-risk users such as executives, journalists, activists, diplomats, and Ukraine-facing personnel for mobile review
- monitor for connections to the infrastructure Google listed, including
snapshare[.]chat,sahibndn[.]io,e5.malaymoil[.]com, andstatic.cdncounter[.]net - update Apple devices to the latest available release as fast as operationally possible
- enable Lockdown Mode for high-risk users if immediate patching is not possible
Detection and response
- treat suspicious mobile browsing activity as a possible incident response case, not just a user-support issue
- look for signs of hidden iframe delivery and abnormal Safari-triggered follow-on activity
- investigate mobile forensic artifacts suggesting access to messages, keychain material, Wi-Fi data, photos, notes, or location history
- watch for evidence that crash logs were deleted, since both GHOSTKNIFE and GHOSTBLADE included cleanup logic
Strategic takeaway
Security teams should fold mobile exploit-chain monitoring into normal threat intelligence work. DarkSword is another reminder that sophisticated mobile intrusion capability can spread faster than many defenders still assume.
Our assessment
DarkSword matters because it shows the industrialization of iPhone exploitation. One exploit chain. Multiple operators. Multiple countries. Multiple payloads. Same basic lesson: if a high-end mobile capability exists in the surveillance ecosystem, defenders should expect it to leak, spread, or be repurposed.
That shifts the defender conversation. The question is no longer whether advanced iOS exploitation can proliferate. It already has. The real question is whether organizations are treating mobile compromise with the urgency they already apply to desktop command-and-control, credential theft, and endpoint intrusion.
What is DarkSword?
DarkSword is a full-chain iOS exploit framework identified by Google that used six vulnerabilities to compromise iPhones and deploy JavaScript payloads with full kernel privileges.
Which iOS versions were affected?
Google says DarkSword supported iOS 18.4 through 18.7. In the campaigns Google observed, UNC6353 activity only supported iOS 18.4 through 18.6, while earlier campaigns also handled iOS 18.7.
Who used DarkSword?
Google linked DarkSword to UNC6748, PARS Defense customers, and UNC6353, a suspected Russian espionage actor.
What malware families were delivered?
Google identified GHOSTKNIFE, GHOSTSABER, and GHOSTBLADE as the final-stage malware families delivered after successful exploitation.
What should defenders do first?
Patch Apple devices quickly, enable Lockdown Mode for high-risk users when needed, monitor for the listed delivery infrastructure, and escalate suspicious iPhone activity into proper mobile investigation workflows.