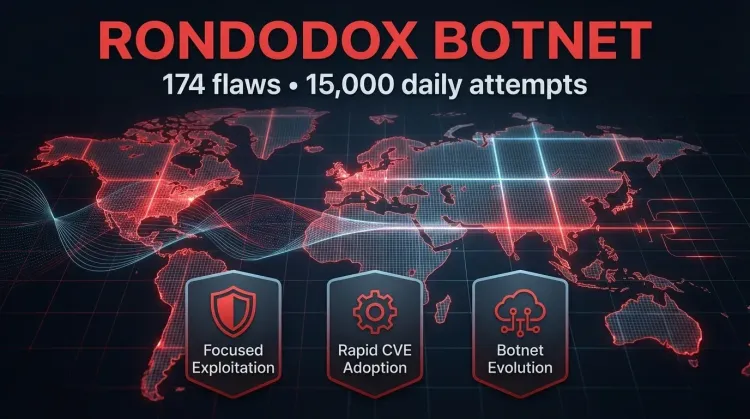
The RondoDox botnet is no longer just another noisy vulnerability spray-and-pray operation. New analysis highlighted by Security Affairs and based on research from Bitsight suggests the botnet has evolved into a more selective exploitation campaign, rotating across 174 vulnerabilities and generating roughly 15,000 exploit attempts per day while increasingly focusing on the flaws that produce results.
That matters because the shift says something important about current botnet tradecraft. The story is not only that RondoDox touches a large number of CVEs. It is that the operators appear to test broadly, discard weak performers, and then concentrate on a smaller set of vulnerabilities that still deliver reliable access. In other words, this looks less like indiscriminate scanning and more like iterative operational tuning.
Why the RondoDox activity stands out
According to Bitsight, researchers mapped 148 CVEs, another 15 public proof-of-concept exploits without CVEs, and 11 exploits that could not be tied to a public proof-of-concept at all. The campaign was observed between May 2025 and February 2026, showing repeated cycles of expansion, pruning, and renewed targeting.
That pattern matters because it reflects a practical attacker workflow: test what is available, keep what works, and rapidly adopt newly disclosed vulnerabilities before defenders can consistently close the window. For defenders, that means the headline number of vulnerabilities matters less than the operator discipline behind the selection process.
A botnet that keeps adapting
RondoDox has already been linked to exploitation of multiple high-profile flaws over time, including:
- CVE-2023-1389 in TP-Link Archer AX21 routers
- CVE-2024-3721
- CVE-2024-12856
- CVE-2025-55182 (React2Shell)
Earlier reporting had already connected the botnet to attacks on routers, DVRs, NVRs, CCTV systems, web servers, and other internet-facing devices. The new analysis adds a more useful insight: the botnet’s infrastructure and exploit selection behavior are evolving, and the operators do not seem interested in keeping every working exploit active forever. They are curating their arsenal.
Why the January 2026 shift matters
One of the most striking observations in the report is the change in early January 2026, when the number of observed vulnerabilities reportedly dropped from around 40 active flaws to just two. One of those was CVE-2025-55182, better known as React2Shell, a vulnerability disclosed in December 2025 and reportedly adopted by the threat actors within days.
That change suggests a move from broad testing to concentration on newer or more operationally useful exploits. This is exactly the kind of shift defenders should pay attention to. A campaign does not need hundreds of active exploits every day to remain dangerous. If operators can narrow their focus to a smaller number of reliable paths, they can reduce noise while preserving impact.
Rapid PoC adoption is the bigger warning sign
Bitsight’s analysis suggests the operators monitor public vulnerability research closely and are quick to incorporate new exploit opportunities, sometimes within weeks and in at least one case even before formal disclosure because a proof-of-concept was already available.
That behavior fits a broader pattern in the current threat intelligence landscape. Public research, exploit code, and rapid weaponization increasingly compress the time between disclosure and active abuse. For organizations with internet-facing infrastructure, the practical implication is simple: patch windows that once felt acceptable may now be too slow.
Not every exploit was polished, but that does not reduce the risk
The researchers also note that execution was not consistently strong. Some exploit implementations appeared incomplete or incorrectly handled, which likely reduced effectiveness. But that does not make the threat less important. It shows that even imperfect operators can remain dangerous when they exploit at scale, monitor public research closely, and continuously refine what works.
For defenders, weak execution by adversaries is not a reliable control. If anything, it means some campaigns will improve over time as operators replace broken techniques with better ones.
Why infrastructure analysis matters here
The report also pushed back on claims that had circulated about RondoDox, including assertions about a supposed loader-as-a-service panel and peer-to-peer command-and-control. Bitsight found that these interpretations were not supported by the evidence. Some allegedly suspicious infrastructure appeared to be simple payload hosting rather than true attacker control systems.
This is an important reminder for incident responders and analysts. Good threat intelligence is not only about collecting indicators. It also requires avoiding overclaiming. Mislabeling infrastructure or repeating weak attribution can send teams in the wrong direction and degrade the quality of detection and response work.
Immediate defensive actions
🔴 Reduce exposure quickly
- Prioritize patching of internet-facing systems tied to newly disclosed or actively weaponized vulnerabilities.
- Review exposure to device classes commonly targeted by botnets, including routers, CCTV infrastructure, DVRs, NVRs, and public web services.
- Remove or isolate assets that no longer need to be publicly reachable.
🟠 Monitor exploit velocity, not just CVE count
- Track how quickly threat actors adopt new proof-of-concept exploits.
- Add monitoring around newly disclosed flaws that attract public exploit code.
- Treat high-volume scanning combined with selective exploitation as an operational signal, not just background noise.
🟡 Improve detection and prioritization
- Correlate scanning activity with public exploit release timelines.
- Hunt for repeated attempts against the specific technologies and services RondoDox has historically targeted.
- Use network segmentation and firewall controls to reduce easy lateral opportunities if internet-facing systems are compromised.
Bottom line
RondoDox shows how botnet operators can evolve from broad opportunistic exploitation to a more selective, efficient model built around rapid testing, rapid adoption, and focused reuse of what works. The risk is not only the number of flaws touched. It is the operational discipline of actors who watch public research, move quickly on fresh vulnerabilities, and refine their exploit set over time.
For defenders, the lesson is clear: reduce exposure, shorten patch response where public exploit code exists, and pay close attention to campaigns that become quieter and more selective rather than assuming that less noise means less risk.