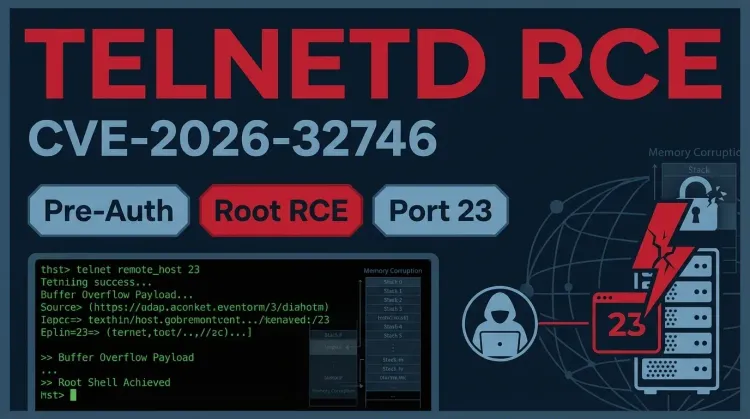
CVE-2026-32746 is a critical flaw in GNU InetUtils telnetd that can allow an unauthenticated remote attacker to execute arbitrary code as root through port 23 before any login prompt appears. According to public reporting and the underlying advisory from Dream, the issue stems from an out-of-bounds write in the LINEMODE Set Local Characters (SLC) suboption handler, creating a buffer overflow condition that can be turned into remote code execution.
The issue reportedly affects all versions of the service through 2.7. That makes it especially relevant for legacy systems and older operational environments where Telnet may still be exposed internally or, in worse cases, reachable from untrusted networks.
Why CVE-2026-32746 matters
This flaw is dangerous because exploitation is pre-authentication. An attacker does not need credentials, user interaction, or a privileged network position. A single crafted connection to port 23 during Telnet option negotiation can be enough to trigger memory corruption before the login process even begins.
For defenders, that creates a severe network security problem. If telnetd is running with root privileges, exploitation can lead directly to full system compromise, opening the door to persistence, lateral movement, and follow-on abuse of the affected host.
The flaw: out-of-bounds write in the SLC handler
At the center of the vulnerability is the way telnetd processes LINEMODE Set Local Characters negotiation during the initial handshake. Dream says the vulnerable code mishandles crafted SLC triplets, leading to an out-of-bounds write and memory corruption before authentication.
In practice, that means the attack lands at one of the worst possible points: early in the connection lifecycle, before traditional login protections or access checks can help.
How the exploit works
- Connect to port 23 on a vulnerable host running GNU InetUtils
telnetd. - Begin Telnet option negotiation as part of the normal handshake sequence.
- Send a crafted SLC suboption payload containing enough malformed triplets to corrupt memory.
- Trigger the out-of-bounds write inside the vulnerable handler.
- Reach code execution as root when the corruption is successfully weaponized.
The key defensive takeaway is simple: this is not a post-login bug. It can be triggered during the protocol handshake itself.
Illustrative description based on the published advisory:
textAttacker connects to port 23 → Telnet option negotiation begins → Crafted LINEMODE SLC data is processed → Out-of-bounds write corrupts memory → Remote code execution may be achieved as root
Why legacy remote access keeps creating risk
Telnet has long been considered unsafe for modern environments because it lacks the protections expected from contemporary remote administration. But this case highlights a second problem beyond plain-text access: legacy services often remain deployed with broad privileges, weak isolation, and little operational scrutiny.
That combination can turn a single vulnerability into a high-impact infrastructure problem. If exposed systems are old, under-monitored, or embedded in critical workflows, even a straightforward service flaw can become a route to wider compromise.
Timeline defenders should know
| Date | Event | Status |
|---|---|---|
| 2026-03-11 | Dream reports CVE-2026-32746 to the vendor/maintainers | ⚠️ Initial disclosure |
| 2026-03-18 | Public reporting highlights unauthenticated root RCE risk in GNU InetUtils telnetd | 📢 Public disclosure |
| 2026-04-01 | Fix expected no later than this date, according to reporting | ✅ Patch expected |
| Ongoing | Organizations assess exposed Telnet services and compensating controls | 🔍 Continuing threat |
Immediate defensive actions
🔴 Exposure reduction
- Disable Telnet wherever it is no longer operationally necessary.
- Block port 23 at the perimeter and with host-based firewall rules.
- Restrict access to any remaining Telnet service to tightly controlled management paths.
- Treat internet-exposed or broadly reachable
telnetdinstances as urgent remediation targets.
🟠 Hardening and containment
- Run
telnetdwithout root privileges where operationally possible. - Segment legacy administration services from broader production networks.
- Review whether Telnet can be replaced fully with SSH or another modern alternative.
- Inspect affected systems for signs of unexpected access or command execution if exposure has existed.
🟡 Detection and validation
- Inventory every system still exposing Telnet internally or externally.
- Hunt for unusual connection attempts to port 23 from untrusted hosts.
- Review legacy systems for weak monitoring coverage and add compensating telemetry where feasible.
- Prioritize incident review if Telnet exposure overlaps with high-value systems or flat network segments.
Simple Linux check to find listening Telnet services:
bashss -ltnp | grep ':23 '
Bottom line
CVE-2026-32746 is a reminder that legacy remote access services can still create modern critical risk. An unauthenticated attacker reaching a vulnerable telnetd instance may be able to trigger root-level remote code execution before login, making exposed port 23 services an immediate priority.
For most teams, the practical response is clear: disable Telnet where possible, isolate what remains, block exposure aggressively, and move fast on remediation once a fix is available.