Executive summary
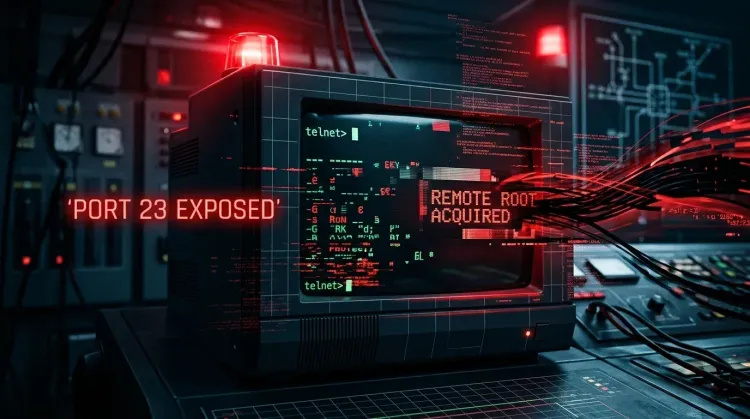
CVE-2026-32746 is the kind of legacy-service bug defenders cannot afford to ignore. The flaw affects GNU Inetutils telnetd through version 2.7 and can be triggered before authentication during Telnet option negotiation. According to the public disclosure, an attacker only needs network access to TCP port 23 and a specially crafted request to corrupt memory and potentially execute code as root.
That combination matters because Telnet still lingers in legacy Linux deployments, embedded devices, and some ICS and OT environments where modernization cycles move slowly. Even if your organization considers Telnet “old news,” exposed telnetd services instantly become high-priority triage items when a no-auth root vulnerability like this appears.
What happened?
Public reporting and the researcher disclosure describe a buffer overflow in the LINEMODE SLC (Set Local Characters) handler inside GNU Inetutils telnetd. In plain English, the service builds a response in a fixed-size buffer during the protocol handshake, but one function keeps appending data without properly checking whether the buffer is already full.
That means an attacker can connect to the service, send a crafted sequence of LINEMODE SLC triplets, and push the daemon into writing past the intended buffer boundary. The issue is hit before any login prompt, so the attacker does not need valid credentials or an authenticated session.
NVD summarizes the flaw as an out-of-bounds write because add_slc does not check whether the internal buffer has room remaining. The GNU mailing-list disclosure goes further and explains how the overflow can corrupt the pointer later used to terminate the suboption, turning memory corruption into a realistic path toward remote code execution.
Why this is more serious than a typical legacy-service flaw
1. It is pre-authentication and network reachable
A single connection to port 23 is reportedly enough to trigger the issue. No login. No user interaction. No post-exploitation foothold required.
2. Root impact is common in real deployments
The public disclosure notes that telnetd often runs with root privileges, especially under inetd or xinetd. That means successful exploitation is not just a service crash scenario; it can become full host compromise.
3. Telnet persists in the worst places to patch quickly
Telnet remains common in older appliances, industrial systems, lab environments, and inherited operational networks. Those are exactly the environments where defenders often face weak network segmentation, long maintenance windows, and operational reluctance to disable legacy protocols.
Technical details in plain English
The vulnerable logic lives in the telnetd SLC handling path. The advisory says the response buffer is fixed at 108 bytes, with only 104 bytes available for data after headers. Each SLC triplet appended by add_slc() consumes more space, but the code does not enforce a proper bound check.
An attacker can exploit that by sending a long LINEMODE SLC suboption with many triplets whose function codes are above the supported range. The daemon then queues repeated “not supported” replies until it overruns the buffer.
Once that overflow occurs, memory adjacent to the buffer can be corrupted, including the pointer used later in the response-building flow. In practice, that creates a plausible route from memory corruption to arbitrary write behavior and ultimately to an exploit that yields remote code execution.
Who should worry most?
The highest-risk environments are:
- Internet-exposed Linux or appliance hosts listening on TCP port 23
- Legacy servers that still ship or enable GNU Inetutils telnetd
- OT and industrial networks where Telnet remains an operational dependency
- Embedded devices and older vendor systems that are costly or slow to upgrade
- Segmented-but-reachable management networks that still permit Telnet from broad internal ranges
If your environment includes legacy remote administration workflows, this is worth treating as an urgent exposure review, not a background patch item.
Immediate actions for defenders
🔴 Find every Telnet listener
Inventory all systems exposing TCP port 23, both externally and internally. Do not assume internal-only exposure is acceptable if large network segments can still reach the service.
🔴 Disable Telnet where possible
If Telnet is not operationally required, remove or disable the service outright. This is the cleanest mitigation while no patch is broadly available.
🔴 Restrict access hard
If you cannot disable it immediately, enforce strict firewall rules, narrow source ranges, and isolate access through dedicated management paths only.
🟠 Reduce privilege where feasible
Where continued use is unavoidable, review whether telnetd can run without root or inside a more constrained execution model.
🟠 Watch for exploitation signals
Prioritize monitoring for malformed Telnet negotiation traffic, crashes, unexplained telnetd restarts, and suspicious child processes spawned around the service.
🟠 Review legacy and industrial exposure separately
ICS and OT teams should assess operational dependencies carefully, because these environments are often where “temporary” Telnet access survives the longest and where a compromise can have disproportionate impact.
Detection ideas
Security teams should look for:
- unexpected traffic to TCP port 23 from unapproved sources
- malformed or unusually long Telnet LINEMODE negotiation sequences
- telnetd crashes, segmentation faults, or abnormal service restarts
- evidence of process execution shortly after inbound Telnet connections
- legacy assets with broad lateral reach inside flat or weakly segmented networks
This is also a good case for combining Internet exposure scanning, internal service discovery, and targeted incident response review on systems that still run Telnet.
Strategic takeaway
The deeper lesson of CVE-2026-32746 is not merely that Telnet is insecure. Everyone already knows that. The real lesson is that legacy protocols become far more dangerous when they remain quietly embedded in hard-to-upgrade environments and inherit privileged execution contexts.
A pre-authentication buffer overflow in a public-facing or broadly reachable Telnet daemon is not a niche issue. It is an avoidable root-compromise path. Teams that still depend on Telnet should use this disclosure as a forcing function to accelerate removal, isolation, or at minimum severe containment.
Is this flaw already patched?
Public reporting says a fix is expected, but the vulnerability was disclosed as unpatched at the time of reporting. Teams should monitor vendor and distribution advisories and deploy the patch as soon as it is available.
Why is port 23 exposure such a big deal here?
Because the bug is reachable during the initial Telnet handshake, attackers do not need valid credentials. If they can connect to port 23, they may be able to trigger the vulnerability directly.
Why are ICS and OT environments highlighted?
Because Telnet still appears in older industrial and operational systems where equipment lifecycles are long, protocol modernization is slow, and compensating controls are often inconsistent.
References
- GNU mailing-list disclosure on the pre-auth buffer overflow.
- NVD entry for CVE-2026-32746.
- Dream Security advisory.
- The Hacker News coverage and exposure context.