The LiteLLM incident is what modern software supply-chain compromise looks like when one poisoned dependency turns into a downstream publisher takeover. According to Snyk, malicious litellm versions 1.82.7 and 1.82.8 were pushed to PyPI after attackers linked to TeamPCP stole the maintainer's publishing credentials through an earlier compromise of Trivy in LiteLLM's CI/CD path.
That makes this more than a bad package release. It is a chained supply-chain attack that moved from a trusted security scanner into a widely used AI gateway library, then into downstream Python environments where the payload could harvest credentials, establish persistence, and attempt lateral movement into Kubernetes infrastructure.
Why this LiteLLM compromise matters
LiteLLM is not a low-impact utility. It is widely used as an LLM gateway and routing layer, often sitting close to API keys, model-provider credentials, CI/CD variables, and cloud access. Snyk says the compromised versions were available for about three hours before PyPI quarantined them, but that short window matters less than the execution model: the payload could trigger during installation or Python startup, not just at normal application runtime.
That makes the exposure profile especially dangerous for build systems, developer workstations, AI tooling, and automation hosts that handle secrets by design.
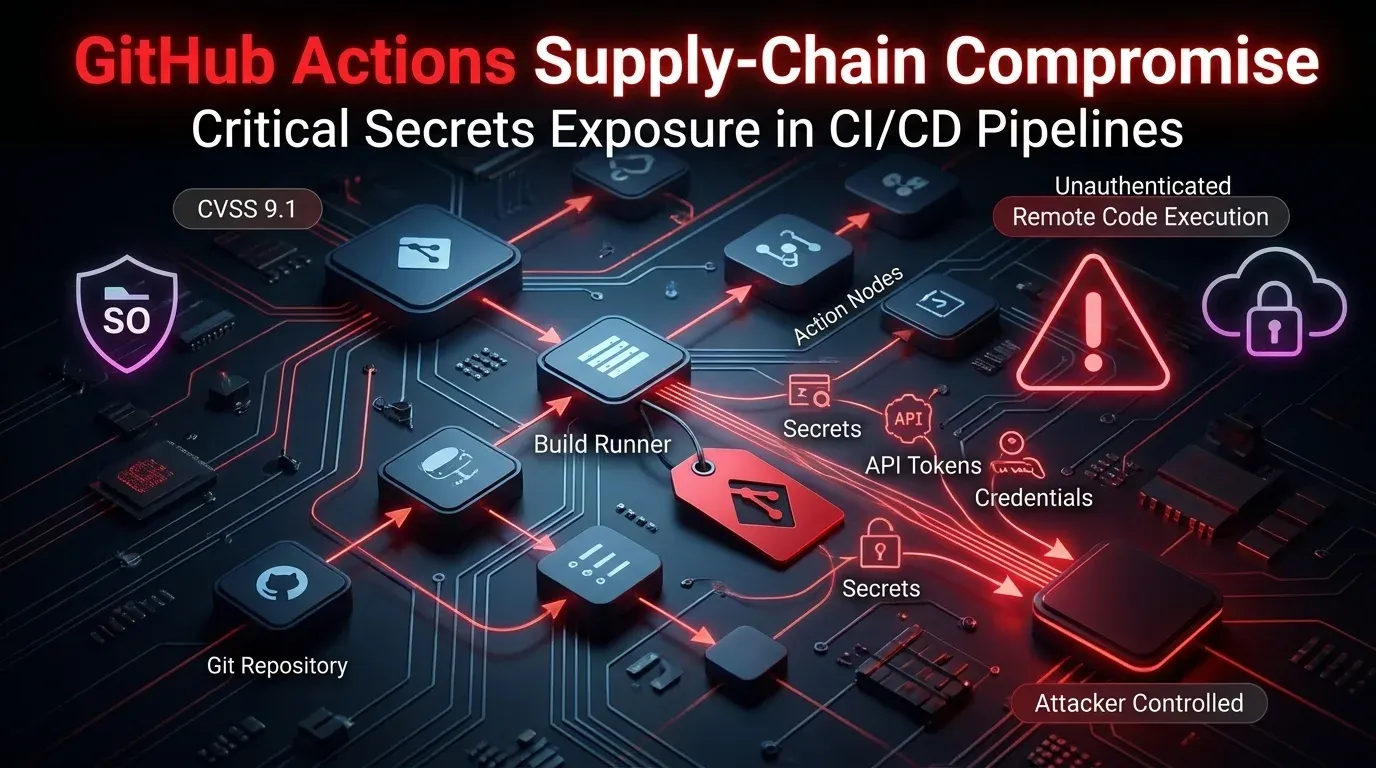
The attack chain: from Trivy to LiteLLM
Snyk's reconstruction points to a sequence defenders should pay close attention to:
- attackers first compromised the Trivy GitHub Action path
- LiteLLM's pipeline pulled that poisoned component during CI/CD
- the malicious action exfiltrated the PyPI publishing token
- attackers published malicious LiteLLM releases to PyPI
- downstream users installed a legitimate-looking package signed with legitimate publisher access
This is exactly the kind of pattern that breaks simplistic integrity assumptions. Package hashes and normal installer checks can still pass when the attacker is publishing through valid credentials. In other words, the trust boundary failed before the package ever reached consumers.
Two malicious delivery methods
The two versions reportedly used different execution paths:
- 1.82.7 embedded malicious code in
proxy_server.py, triggering when LiteLLM proxy components were imported - 1.82.8 used a
.pthstartup hook, which is even more dangerous because it can fire on Python interpreter startup without waiting for a specific import path
That second technique matters a lot. A malicious .pth file can execute during pip operations, local tooling startup, IDE behavior, and CI tasks. This turns a package compromise into a broader Python runtime trust problem, not just an application dependency problem.
What the payload reportedly did
Snyk describes a multi-stage payload designed for real operational abuse, not a simple proof of concept. Reported behaviors included:
- harvesting SSH keys, cloud credentials, CI/CD secrets,
.envfiles, Git credentials, and webhook tokens - encrypting and exfiltrating collected data to attacker infrastructure
- installing persistence under a fake telemetry-style service name
- reading Kubernetes service account context and attempting cluster-wide secret access
- attempting node-level spread through privileged pods in
kube-system
That mix of credential theft, persistence, and Kubernetes-aware follow-on behavior is what turns this into a serious enterprise incident. The package did not just expose one application. It targeted the environment around the application.
Why this is a stronger warning for AI infrastructure teams
LiteLLM is increasingly deployed as a centralized broker for multiple model backends. In many environments, that means one host can hold access to OpenAI-style providers, cloud model APIs, internal routing secrets, and sometimes orchestration credentials. When an AI gateway becomes the compromised package, the blast radius can be wider than in a typical Python library incident.
The broader lesson is not “AI tooling is risky” in the abstract. It is that tools wired into high-trust automation paths deserve the same scrutiny as identity systems, CI/CD controllers, and security scanners. Once one of those layers is compromised, ordinary package verification is not enough.
What defenders should do now
1. Treat affected installs as compromise, not simple vulnerability
If any environment installed litellm 1.82.7 or 1.82.8, do not treat the fix as a normal version bump. Assume the payload may already have run.
2. Hunt for persistence and startup-hook abuse
Check for:
- suspicious
.pthfiles in Python environments - unexpected files under user config paths such as
~/.config/ - fake telemetry/system-monitor style services
- evidence of Python subprocess chains that should not exist
3. Rotate exposed secrets aggressively
Prioritize rotation of:
- SSH keys
- API keys
- cloud credentials
- CI/CD tokens
- Git and registry credentials
- Kubernetes and container-related secrets
4. Review cluster exposure
If any affected host had Kubernetes access, inspect for unusual secret reads, privileged pod launches, or suspicious node-setup-* style activity in kube-system.
5. Reassess transitive trust in pipeline tooling
The most important upstream lesson here is that a poisoned security scanner can become an attack delivery vehicle. Review how CI/CD pulls scanners, actions, and helper tools, especially when version pinning or provenance controls are weak.
Strategic takeaway
The LiteLLM compromise shows how modern software supply-chain attacks keep evolving: attackers do not need to break the package index if they can poison the build path and steal legitimate publisher credentials first. Once that happens, malicious code arrives through channels most defenders still instinctively trust.
For security teams, the real story is not just LiteLLM. It is the chained trust failure across scanner, pipeline, publisher, package index, and downstream runtime.
Bottom line
If you installed LiteLLM 1.82.7 or 1.82.8, treat the host as potentially compromised, rotate secrets, inspect for persistence, and investigate whether the poisoned Trivy-to-PyPI chain exposed broader CI/CD or Kubernetes trust paths.
Key takeaways
✅ This was a chained supply-chain attack — a poisoned upstream scanner appears to have led to stolen publishing credentials and malicious PyPI releases.
✅ The payload was built for real post-compromise use — credential theft, encrypted exfiltration, persistence, and Kubernetes-aware spread were all part of the reported behavior.
✅ Package integrity checks are not enough when publisher trust fails — signed or correctly hashed artifacts can still be malicious if legitimate credentials were stolen first.