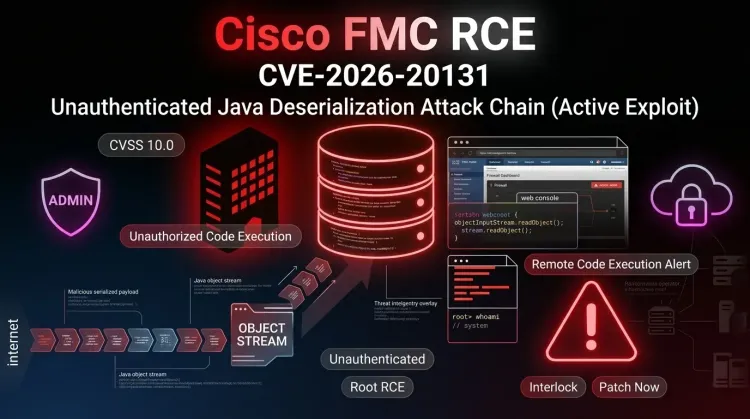
CVE-2026-20131 is the kind of firewall-management flaw defenders dread: an unauthenticated bug in Cisco Secure Firewall Management Center (FMC) that can let a remote attacker execute arbitrary Java code as root. Cisco says the issue stems from insecure deserialization in the web-based management interface. AWS then added the operational punchline: Interlock ransomware operators were already exploiting it 36 days before public disclosure.
That combination matters. A maximum-severity flaw on a security management platform is already dangerous. When active exploitation begins before defenders even know the bug exists, the conversation shifts from patch hygiene to incident response. Teams now have to ask not only whether they upgraded, but whether exposed FMC systems were already touched, staged, or used as a launch point for deeper compromise.
Why CVE-2026-20131 matters
Cisco Secure Firewall Management Center is not just another web app. It is a control plane for firewall policy, visibility, and device administration. If an attacker gains code execution there, the blast radius can extend well beyond the host itself.
Cisco’s advisory says exploitation is possible by sending a crafted serialized Java object to the vulnerable web interface. A successful exploit can yield arbitrary code execution with root privileges. Cisco also notes that the attack surface is reduced when the FMC management interface is not exposed to the public internet, but there is no workaround that truly fixes the issue short of patching.
In plain terms, the risk looks like this:
- the attacker reaches the web-based FMC management interface
- a crafted request abuses insecure deserialization
- arbitrary Java code executes on the appliance
- the attacker gains root-level control
- that foothold can support credential theft, tooling deployment, persistence, and lateral movement
That last point is what turns this from “just another Cisco advisory” into a serious operational problem. A compromised firewall management system sits close to policy, segmentation, and trust boundaries. For defenders, that means a single Internet-facing admin surface can become a privileged beachhead.
What AWS observed about Interlock
The AWS Security Blog adds the most useful field context so far. According to Amazon threat intelligence, activity tied to this flaw was already visible from January 26, 2026, long before Cisco published the advisory on March 4. AWS says it used its MadPot sensor network to identify exploit attempts and then gained visibility into the next stages of the intrusion chain.
The standout point is not only that exploitation started early. It is that AWS linked the activity to Interlock ransomware, an operator already associated with real-world intrusions and post-compromise tooling. AWS says a misconfigured attacker staging server exposed a larger toolkit, including custom remote access trojans, reconnaissance scripts, and infrastructure used to support the campaign.
That matters because it frames CVE-2026-20131 as more than an opportunistic scan-and-drop issue. The reported activity suggests a structured intrusion path:
- exploit the exposed FMC management plane
- validate code execution and trigger callbacks
- pull secondary payloads from attacker infrastructure
- run host and network reconnaissance
- prepare for broader access, exfiltration, and ransomware operations
This is a classic example of threat intelligence turning a vulnerability story into a defender decision story. The key question is no longer “is the bug real?” It is “what should we assume an attacker did with that foothold?”
Timeline from zero-day use to public action
| Date (UTC) | Event | Status |
|---|---|---|
| January 26, 2026 | AWS says Interlock activity tied to the flaw begins | 🔴 Zero-day exploitation |
| March 4, 2026 | Cisco publishes advisory and patches CVE-2026-20131 | 📢 Public disclosure |
| March 18, 2026 | Cisco updates the advisory to acknowledge attempted exploitation | ⚠️ Exploitation confirmed |
| March 18, 2026 | AWS publishes threat research on Interlock targeting enterprise firewalls | 🔍 Operational context |
| March 2026 | Defenders are pushed from routine patching into compromise assessment | 🚨 Urgent response |
Why exposed management planes keep getting punished
Security teams sometimes focus hard on protecting user-facing services while management interfaces stay reachable from broad networks “for convenience.” That is exactly the kind of decision flaws like this punish.
Cisco explicitly notes that public internet exposure increases the attack surface. Once a management plane is reachable, a bug in authentication, serialization, or session handling can bypass the normal safety assumptions defenders place around internal admin tools.
For firewall and security-management platforms, the stakes are even higher because they often hold:
- administrative secrets and integration credentials
- asset visibility data and policy context
- routes to downstream appliances and trusts
- operational information useful for ransomware staging
This is where network segmentation becomes more than a best-practice slogan. If the management interface is reachable from the wrong places, a single flaw can collapse the defensive moat it was supposed to help enforce.
Immediate defensive actions
1. Patch Cisco FMC immediately
If your environment runs a vulnerable Cisco Secure Firewall Management Center release, move the upgrade to the front of the queue. Cisco has released fixed software and says there are no real workarounds.
2. Treat public exposure as a serious risk multiplier
If the FMC management interface was reachable from the internet or from overly broad network segments, do not stop at patch verification. That exposure changes the probability that compromise already happened.
3. Hunt for evidence of exploitation and follow-on activity
Look for:
- suspicious HTTP requests to the FMC web interface
- unexpected process execution or child processes from the management service
- outbound callbacks to unknown infrastructure
- newly dropped tools, staging artifacts, or reconnaissance output
- signs of credential abuse, policy manipulation, or unusual administrator actions
4. Review downstream trust and credentials
Because the affected platform is high-privilege, defenders should review what credentials, integrations, or network paths may have been reachable from the appliance. If compromise is suspected, rotate what matters.
5. Revisit how management planes are exposed
A firewall manager should not itself be casually exposed. Limit access, require strong administrative controls, and reduce the set of networks that can reach it.
Strategic takeaway
CVE-2026-20131 is not only a Cisco patch story. It is a reminder that security infrastructure is still just software, and when that software is exposed, attackers get a shot at some of the most privileged systems in the environment.
The extra sting here is the timeline. If AWS is right, defenders were already behind before the advisory existed. That means organizations should think in two phases: first, patch urgently; second, assess whether this should be handled as a potential intrusion rather than a clean maintenance task.
Bottom line
Patch Cisco FMC now, assume public exposure raises compromise odds, and investigate whether Interlock-style post-exploitation activity touched the environment before disclosure.
Key takeaways
✅ The flaw is unauthenticated and high impact — a crafted request to the web interface can lead to root-level code execution.
✅ This was not merely theoretical risk — AWS says Interlock exploited the flaw 36 days before public disclosure.
✅ The real danger is what comes next — once a firewall management plane falls, attackers gain a privileged foothold for reconnaissance, persistence, and broader compromise.
If Cisco FMC was exposed in your environment, do not treat CVE-2026-20131 as routine patching. Treat it as a patch-plus-investigate event.
References
- Cisco Security Advisory - Cisco Secure Firewall Management Center Software Remote Code Execution Vulnerability
- AWS Security Blog - Amazon threat intelligence teams identify Interlock ransomware campaign targeting enterprise firewalls
- BleepingComputer - Ransomware gang exploits Cisco flaw in zero-day attacks since January