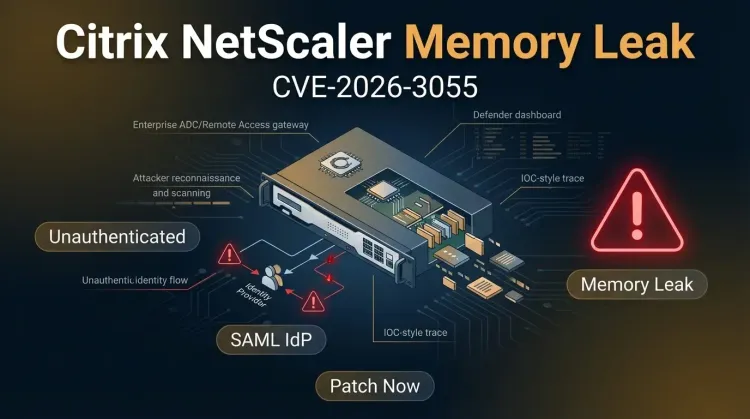
CVE-2026-3055 puts Citrix NetScaler ADC and NetScaler Gateway defenders back in a familiar, uncomfortable place: internet-facing edge infrastructure, a critical memory disclosure bug, and a narrow configuration detail that many real-world environments may already rely on. Citrix says the flaw is an out-of-bounds read with a CVSS 9.3 score that can let an unauthenticated remote attacker leak sensitive data from appliance memory.
The limiting condition matters, but it does not make this a niche issue. Citrix says systems are vulnerable when they are configured as a SAML Identity Provider, while default configurations are not affected. In practice, that means organizations using NetScaler as part of a federated authentication or single sign-on workflow need to treat this as an urgent exposure review, not a routine maintenance item.
Why CVE-2026-3055 matters
An out-of-bounds read is often underestimated because it is “only” a read primitive, not immediate code execution. On a security appliance, that distinction can be dangerously misleading. If an unauthenticated attacker can repeatedly pull data from memory, the real question becomes what secrets, session material, or internal state may be exposed over time.
For NetScaler appliances sitting near authentication and application access flows, leaked memory can potentially expose:
- active session material
- authentication-related secrets
- user or tenant data in transit through the appliance
- configuration details useful for follow-on intrusion
That is why the story resonates beyond the technical bug class. When edge identity infrastructure leaks memory, defenders have to think about access paths, identity trust, and what secondary abuse might follow once enough data has been harvested.
The risky configuration: SAML IdP
Citrix says the vulnerable condition is specifically tied to devices configured as a SAML Identity Provider. Rapid7 notes this may be a common setup for organizations using enterprise authentication and single sign-on patterns. Citrix also gave defenders a practical way to check exposure by reviewing configuration for the relevant add authentication samlIdPProfile string.
That detail matters operationally because it lets teams move fast:
- identify whether the appliance is customer-managed and in scope
- confirm whether SAML IdP is enabled
- upgrade affected systems to fixed builds
- review logs and access patterns for suspicious requests against exposed appliances
This is also a reminder that edge systems tied to identity are not just network plumbing. They are part of the organization's access control surface. A weakness there can quickly become a broader identity and session exposure problem.
Affected versions and fixes
According to Rapid7's summary of the Citrix advisory, affected releases include:
- NetScaler ADC and NetScaler Gateway 14.1 before 14.1-66.59
- NetScaler ADC and NetScaler Gateway 13.1 before 13.1-62.23
- NetScaler ADC 13.1-FIPS and 13.1-NDcPP before 13.1-37.262
Citrix says customer-managed instances are affected, while cloud instances managed directly by Citrix are not.
At publication time, reporting indicated there was no confirmed in-the-wild exploitation and no public proof-of-concept. That is good news, but not a reason to slow down. High-severity edge bugs tend to become far more dangerous once public analysis, exploit code, or scanning logic appears.
Why defenders will compare this to CitrixBleed
Rapid7 explicitly pointed to the historical context: Citrix memory disclosure bugs have a way of becoming major incidents once the wider ecosystem catches up. The obvious comparison is CitrixBleed (CVE-2023-4966), which became broadly exploited after many organizations underestimated how quickly session theft risk could translate into real compromise.
That does not mean CVE-2026-3055 is a replay of the same intrusion pattern. It does mean defenders should avoid the old mistake of hearing “memory leak” and assuming the impact is abstract. On internet-facing infrastructure that mediates identity and remote access, memory disclosure can become a stepping stone to session abuse, account compromise, and broader lateral movement.
What defenders should do now
1. Patch affected appliances immediately
If you run customer-managed NetScaler ADC or Gateway instances in the affected version ranges, prioritize upgrades now.
2. Verify whether SAML IdP is enabled
Do not assume your deployment is safe because the vulnerable condition is configuration-dependent. Confirm it directly.
3. Review exposure of internet-facing appliances
If these systems are reachable from the public internet, assume scanning and opportunistic targeting will accelerate now that the bug is public.
4. Hunt for suspicious requests and anomalous auth behavior
Look for:
- unusual requests against SAML-related endpoints
- spikes in appliance errors or crashes
- suspicious authentication activity after edge access events
- signs of session misuse or unexpected logins
5. Reassess blast radius around identity infrastructure
Even without confirmed active exploitation, this is a good moment to revisit network placement, monitoring, and credential/session assumptions around NetScaler deployments. Identity-adjacent edge systems deserve the same rigor as other high-value control points.
Strategic takeaway
CVE-2026-3055 is a patch-now issue not because exploitation is already proven, but because the affected technology sits at a dangerous intersection of internet exposure, identity handling, and sensitive in-memory data. The SAML IdP requirement narrows the vulnerable set, yet it may still describe a large number of enterprise deployments.
For defenders, the right mindset is simple: treat this as a short window to get ahead of the next wave. Once exploit logic or mass scanning catches up, the conversation will stop being about configuration nuance and start being about which organizations moved fast enough.
Bottom line
If your NetScaler environment uses SAML IdP, patch CVE-2026-3055 urgently and review the appliance as identity-critical edge infrastructure, not just another network component.
Key takeaways
✅ The flaw is critical and unauthenticated — remote attackers can leak sensitive appliance memory without logging in.
✅ Exposure depends on SAML IdP configuration — default setups are not affected, but many real enterprise deployments may be.
✅ The risk is what memory disclosure can unlock next — session theft, auth abuse, and follow-on compromise are the real defender concern.