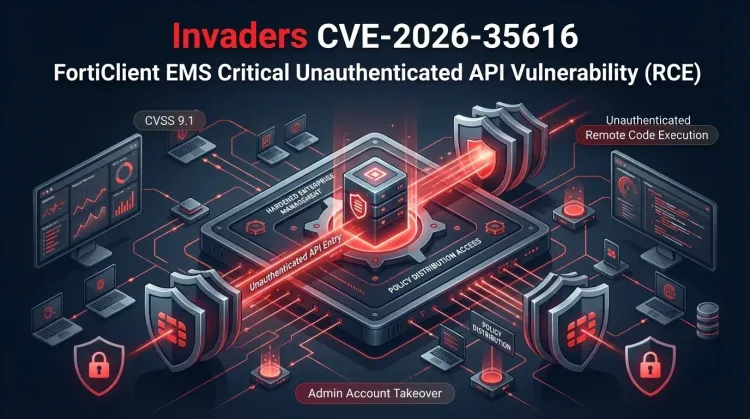
CVE-2026-35616 is the second serious FortiClient EMS story in less than two weeks, and that alone should change how defenders prioritize it. Fortinet issued out-of-band hotfixes for an improper access control bug in FortiClient Endpoint Management Server (EMS) 7.4.5 and 7.4.6. Public reporting and researcher statements say the flaw has already been exploited, while Fortinet has pushed customers toward emergency fixes and the upcoming 7.4.7 release.
The important lesson is not just that another high-severity vulnerability hit FortiClient EMS. It is that an unauthenticated API authentication and authorization bypass in an exposed endpoint management tier creates immediate management-plane risk. When attackers can reach the server before login, the problem is no longer just patch hygiene. It becomes a potential incident response event.
Why this FortiClient EMS flaw matters
FortiClient EMS is not a low-value application. It is a centralized control point used to enroll endpoints, distribute security policy, manage certificates, and maintain visibility across managed devices. That makes it part of the high-trust administrative layer of an enterprise attack surface.
According to Fortinet and third-party reporting, CVE-2026-35616 is an improper access control issue that can allow an unauthenticated attacker to bypass API authentication and authorization controls with crafted requests. Public summaries describe the likely impact as unauthorized code or command execution on the vulnerable host.
That combination matters for two reasons:
- the vulnerable component is exposed through a network-facing API
- the product itself manages security posture across downstream endpoints
In practice, a compromise at that layer can quickly move beyond one server and into wider trust, policy, and credential risk.
What is known so far
Fortinet’s advisory says the issue affects FortiClient EMS 7.4.5 through 7.4.6 and that the 7.2 branch is not affected. The company says the flaw will also be fixed in 7.4.7 and has released hotfix guidance for affected builds.
Public reporting from BleepingComputer and Help Net Security says researchers at Defused observed exploitation activity and framed the weakness as a pre-authentication API access bypass. runZero also highlighted that more than 2,000 internet-exposed FortiClient EMS instances were visible online, which gives defenders a useful reminder: even if only a subset is actually vulnerable, the product is discoverable at scale.
One detail worth noting is that the public messaging has not been perfectly aligned. Third-party reporting describes active exploitation, while the scraped Fortinet advisory view is less explicit in the summary text. Defenders should not wait for perfect wording convergence before acting. Weekend hotfixes for a critical unauthenticated management-plane bug are enough reason to move fast.
Why pre-auth management-plane bugs are especially dangerous
A bug like CVE-2026-35616 is more serious than an ordinary web application flaw because of what FortiClient EMS controls.
If attackers gain access to the EMS layer, the downstream risk can include:
- visibility into enrolled devices and administrative workflows
- abuse of policies, packages, or server-side trust relationships
- theft or misuse of credentials and tokens associated with endpoint operations
- a starting point for broader lateral movement or security-tool tampering
That is why this should be treated as management-plane exposure. Security tooling can become a force multiplier for attackers when it is both internet-reachable and highly trusted.
Immediate actions for defenders
🔴 Patch affected EMS versions now
- Identify every FortiClient EMS deployment in production, staging, and recovery environments.
- If you are running 7.4.5 or 7.4.6, apply the vendor hotfix immediately.
- Plan upgrade to 7.4.7 or later as soon as it is available in your validated release path.
🔴 Treat exposed EMS servers as potential incident candidates
- Review internet-facing EMS instances first.
- Check administrative activity, unexpected process execution, and unusual API behavior around the disclosure window.
- Preserve logs before cleanup if compromise is suspected.
🟠 Reduce unnecessary exposure
- Remove direct public access to EMS wherever possible.
- Put administrative interfaces behind VPN, bastion, or tightly controlled access control paths.
- Reassess network segmentation so compromise of a management server does not automatically expand into wider enterprise control.
🟠 Re-check trust tied to the platform
- Review what certificates, service accounts, software distribution paths, and admin roles depend on the EMS server.
- If exposure has been long-lived, consider whether credentials or trust artifacts should be rotated.
- Validate whether security agents received any unexpected policy or package changes.
Strategic takeaway
CVE-2026-35616 is a reminder that endpoint management infrastructure deserves the same urgency defenders already apply to edge appliances and identity systems. A critical unauthenticated API bypass on a product that governs endpoint trust should move straight into the highest operational queue.
For FortiClient EMS users, the decision path is straightforward: patch 7.4.5 and 7.4.6 immediately, remove unnecessary exposure, and investigate exposed servers as though they may already need containment. When the vulnerable system is the one managing your security agents, delaying the response is the real risk multiplier.
What is CVE-2026-35616?
CVE-2026-35616 is a critical improper access control vulnerability in Fortinet FortiClient EMS. Public reporting says it enables a pre-authentication API authentication and authorization bypass that can lead to unauthorized code or command execution.
Which versions are affected?
Fortinet says FortiClient EMS 7.4.5 through 7.4.6 are affected. The 7.2 branch is not affected, and 7.4.7 is expected to include the fix.
Why is this flaw so high priority?
Because FortiClient EMS is a high-trust management platform for endpoints. If attackers compromise that server, the impact can extend into policy control, credentials, and downstream security operations.
What should defenders do first?
Patch affected servers immediately, prioritize any internet-exposed EMS instances, and review those systems for signs of suspicious API activity or unauthorized administrative actions.