#Incident Response
GitHub GHES Signing Key Rotation Puts Admins on the Clock
GitHub GHES Signing Key Rotation Puts Admins on the Clock Executive Summary GitHub warned on May 26, 2026 that administrators running GitHub Enterprise Server (...
Lucas Oliveira
Research
Dirty Frag Linux kernel zero-day gives local users a fast path to root
Dirty Frag Linux kernel zero-day gives local users a fast path to root Dirty Frag is the kind of Linux bug defenders worry about because it turns a limited foot...
Lucas Oliveira
Research
Dirty Frag Linux kernel zero-day gives local users a fast path to root
Dirty Frag Linux kernel zero-day gives local users a fast path to root Dirty Frag deserves attention because it is not a theoretical Linux bug waiting for slow...
Lucas Oliveira
Research
CVE-2026-0300 puts exposed PAN-OS User-ID portals on a zero-day attack path
CVE-2026-0300 puts exposed PAN-OS User-ID portals on a zero-day attack path A critical point in the new PAN-OS warning is that defenders are not looking at a ro...
Lucas Oliveira
Research
DAEMON Tools supply-chain attack turns trusted installers into a malware delivery path
DAEMON Tools supply-chain attack turns trusted installers into a malware delivery path The most important part of the DAEMON Tools incident is not that malware...
Lucas Oliveira
Research
BlackCat case shows ransomware risk inside trusted cyber roles
BlackCat case shows ransomware risk inside trusted cyber roles A new U.S. criminal case tied to BlackCat (ALPHV) is a sharp reminder that ransomware risk is not...
Lucas Oliveira
Research
Firestarter leaves patched Cisco firewalls at continued risk
Firestarter leaves patched Cisco firewalls at continued risk A newly detailed persistence mechanism called Firestarter changes the defender story around last ye...
Lucas Oliveira
Research
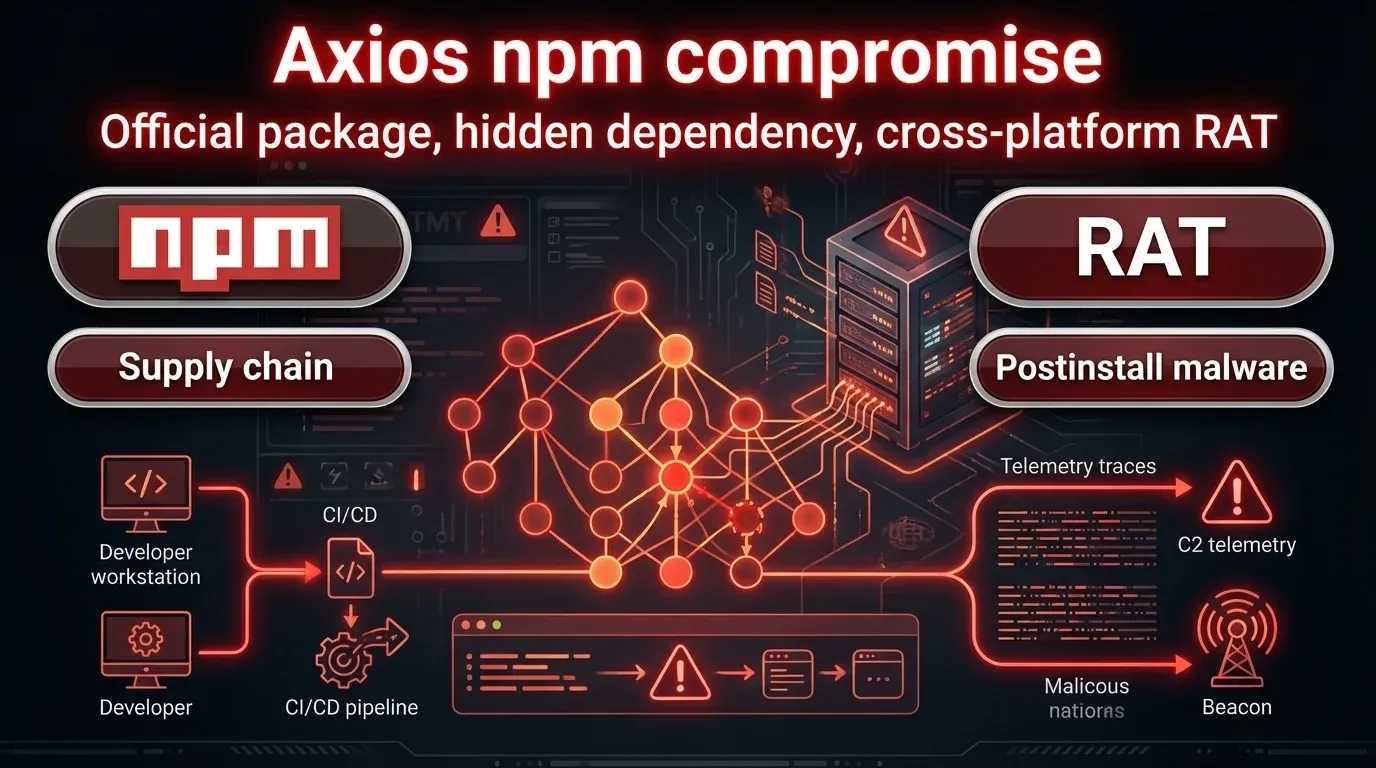
Axios npm compromise pushed a cross-platform RAT through a fake dependency
Axios npm compromise pushed a cross-platform RAT through a fake dependency A compromise of the widely used axios package on npm shows why defenders cannot rely...
Lucas Oliveira
Research
FBI seizes Handala sites after destructive Stryker hack
FBI seizes Handala sites after destructive Stryker hack | 2026 Executive Summary The FBI and U.S. Department of Justice have seized two websites linked to Handa...
Lucas Oliveira
Research
CVE-2025-26399: SolarWinds WHD Exploitation Hits Servers
CVE-2025-26399: SolarWinds WHD Exploitation Hits Servers | 2026 Executive Summary CVE-2025-26399 in SolarWinds Web Help Desk has moved from “critical but patcha...
Lucas Oliveira
Research
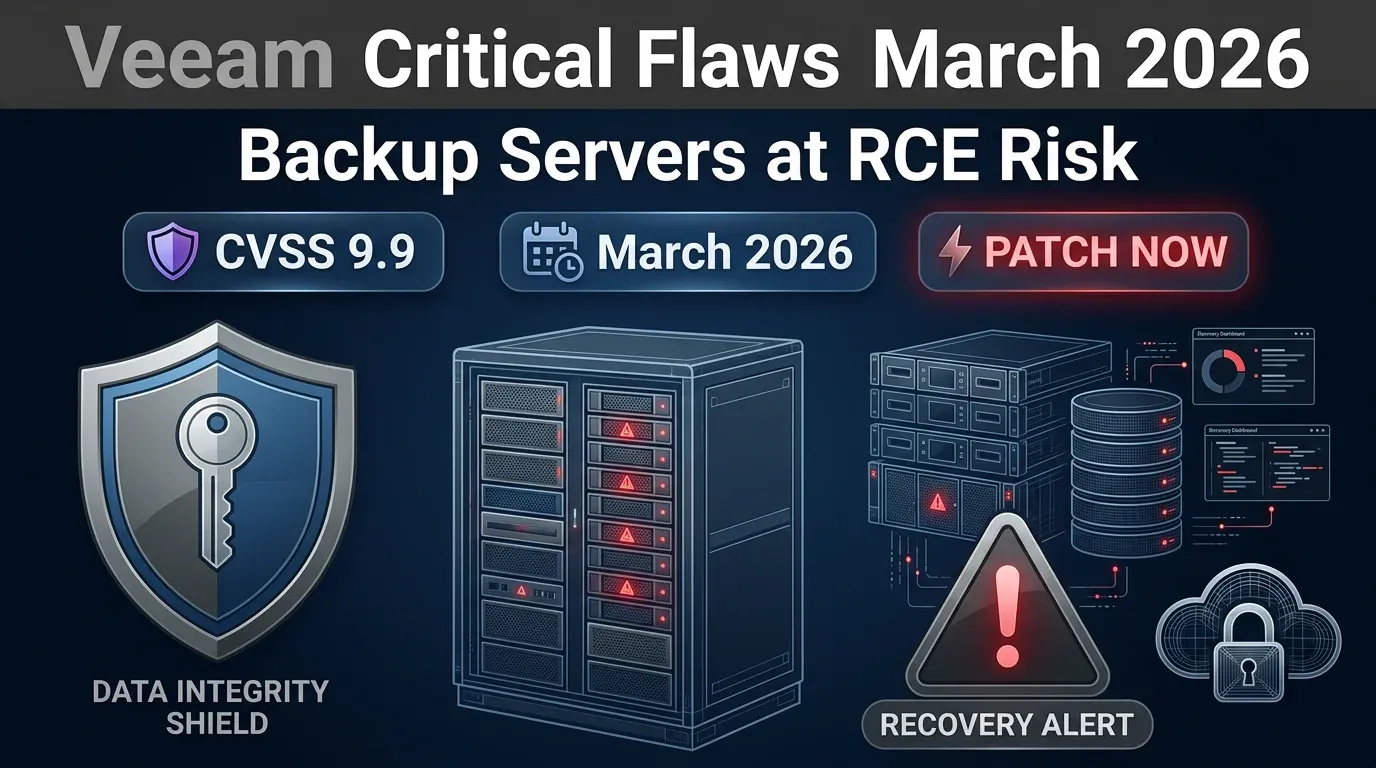
Veeam patches critical backup server flaws with RCE risk
Veeam patches critical backup server flaws with RCE risk Veeam’s March 2026 security update deserves immediate attention from enterprise defenders. The company...
Lucas Oliveira
Research
TELUS Digital breach: ShinyHunters claims 1PB data theft
TELUS Digital breach: ShinyHunters claims 1PB data theft | 2026 Executive Summary TELUS Digital confirmed on March 12, 2026 that it is investigating unauthorize...
Lucas Oliveira
Research